Youtube search...
NOTE: Not necessarily restricted to artificial intelligence-based solutions.
Important Tools
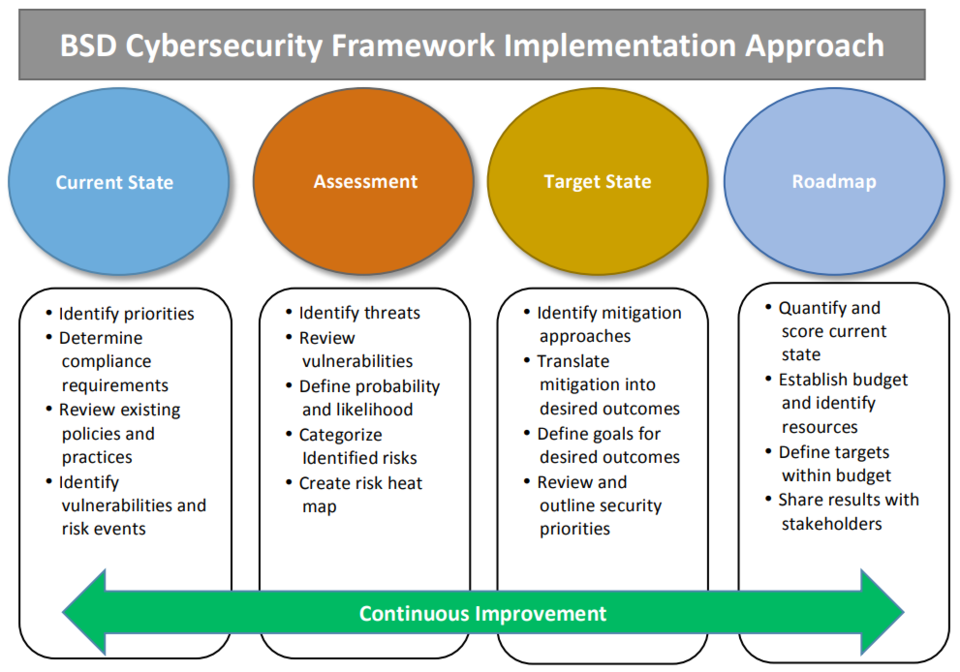
Cybersecurity frameworks, architectures and roadmaps are important tools for organizations to improve their security posture and manage cyber risks. Here is some information about them from various sources:
Cybersecurity Frameworks
A cybersecurity framework is a set of standards, guidelines and best practices that help organizations to assess and improve their ability to prevent, detect and respond to cyber threats. A cybersecurity framework can help organizations to:
- Define their current and desired security state
- Identify and prioritize gaps and risks
- Align security activities with business goals and requirements
- Communicate and collaborate with internal and external stakeholders
- Demonstrate compliance with regulations and industry standards
Some examples of cybersecurity frameworks are:
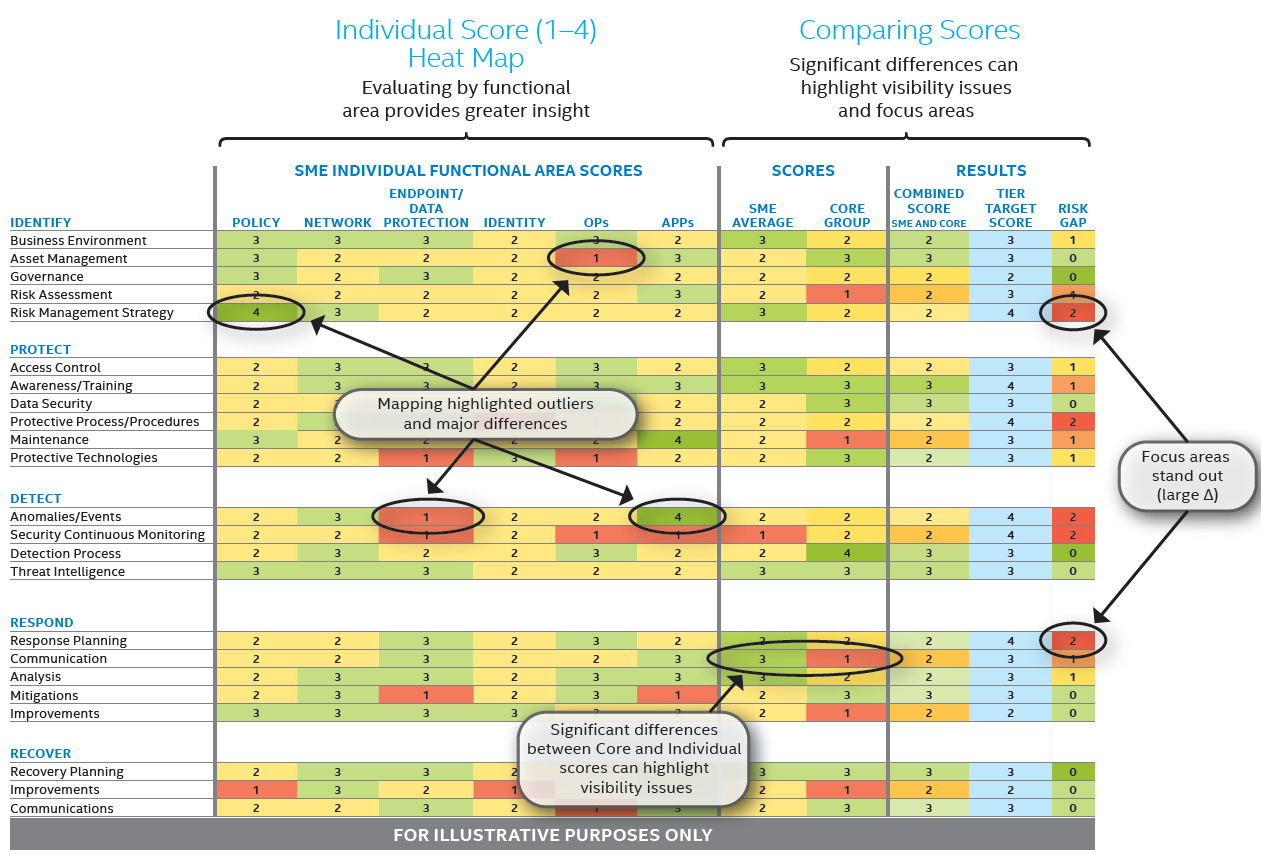
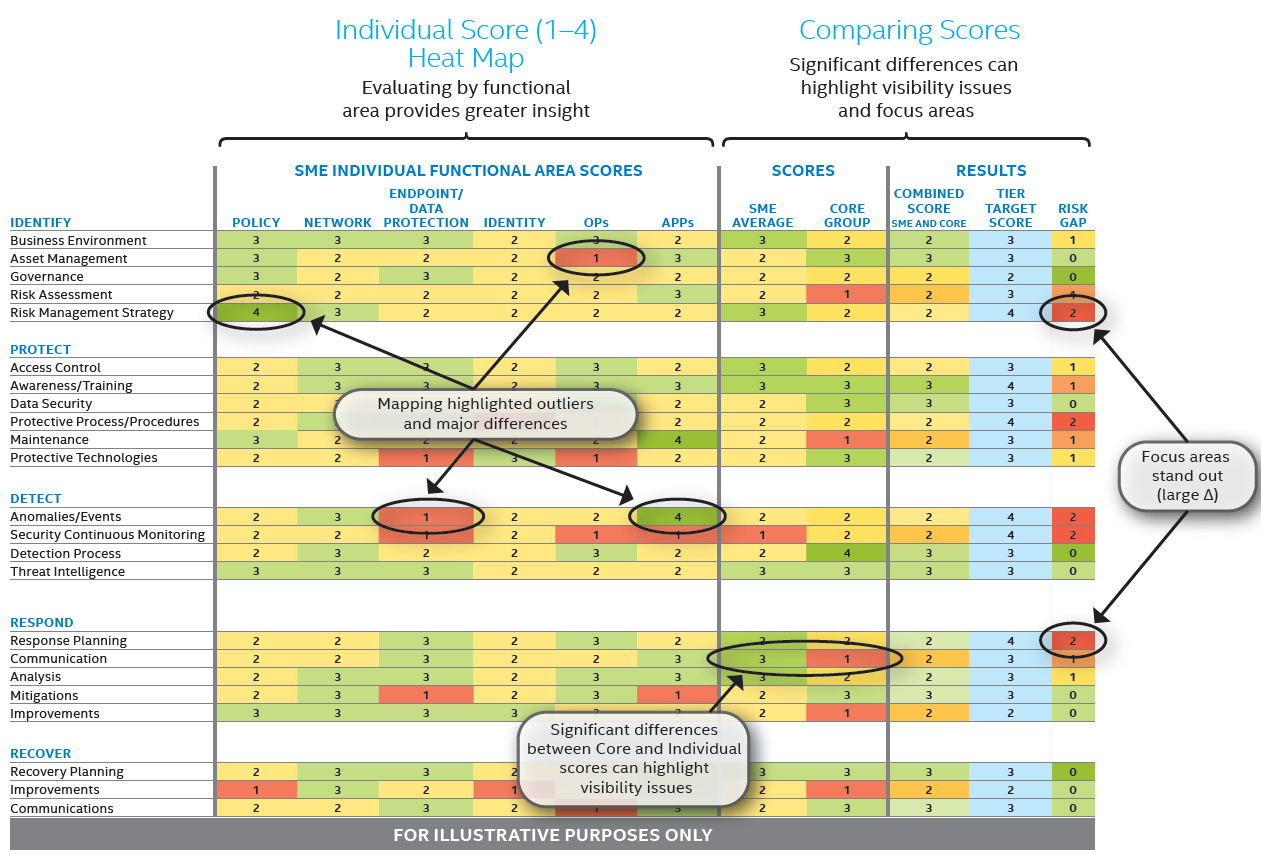
- NIST Cybersecurity Framework (CSF): A voluntary framework developed by the National Institute of Standards and Technology (NIST) for critical infrastructure sectors in the US, but widely adopted by other sectors and countries as well. The CSF consists of five core functions: Identify, Protect, Detect, Respond and Recover. Each function has a set of categories, subcategories and informative references that provide guidance on specific security outcomes.
- NIST Cybersecurity Framework 2.0 Reference Tool | NIST ... allows users to explore the Draft CSF 2.0 Core (Functions, Categories, Subcategories, Implementation Examples) and offers human and machine-readable versions of the draft Core (in both JSON and Excel formats). Currently, the tool allows users to view and export portions of the Core using key search terms. This tool will ultimately enable users to create their own version of the CSF 2.0 Core with selected Informative References and will provide a simple and streamlined way for users to explore different aspects of the CSF Core.
- ISO/IEC 27001: An international standard for information security management systems (ISMS) that specifies the requirements for establishing, implementing, maintaining and improving an ISMS. The standard covers all aspects of information security, including risk assessment, policies, procedures, controls, monitoring, auditing and improvement. The standard also provides a certification scheme for organizations that want to demonstrate their compliance.
- CIS Controls: A set of 20 prioritized and actionable security controls developed by the Center for Internet Security (CIS) based on the most common and effective practices observed in real-world incidents. The CIS Controls cover both technical and organizational aspects of security, such as inventory, configuration, vulnerability management, access control, incident response and awareness training. The CIS Controls also provide implementation guidance for different types of organizations, such as small businesses, enterprises and cloud environments.
Cybersecurity Architectures
A cybersecurity architecture is a design or blueprint that describes how security components and processes are organized, integrated and configured to protect an organization's assets, data and operations from cyber threats. A cybersecurity architecture can help organizations to:
- Define the scope and boundaries of their security domain
- Identify and classify their assets, data and operations
- Select and implement appropriate security controls and technologies
- Define roles and responsibilities for security management and operations
- Establish security policies, standards and procedures
- Monitor and measure security performance and effectiveness
Some examples of cybersecurity architectures are:
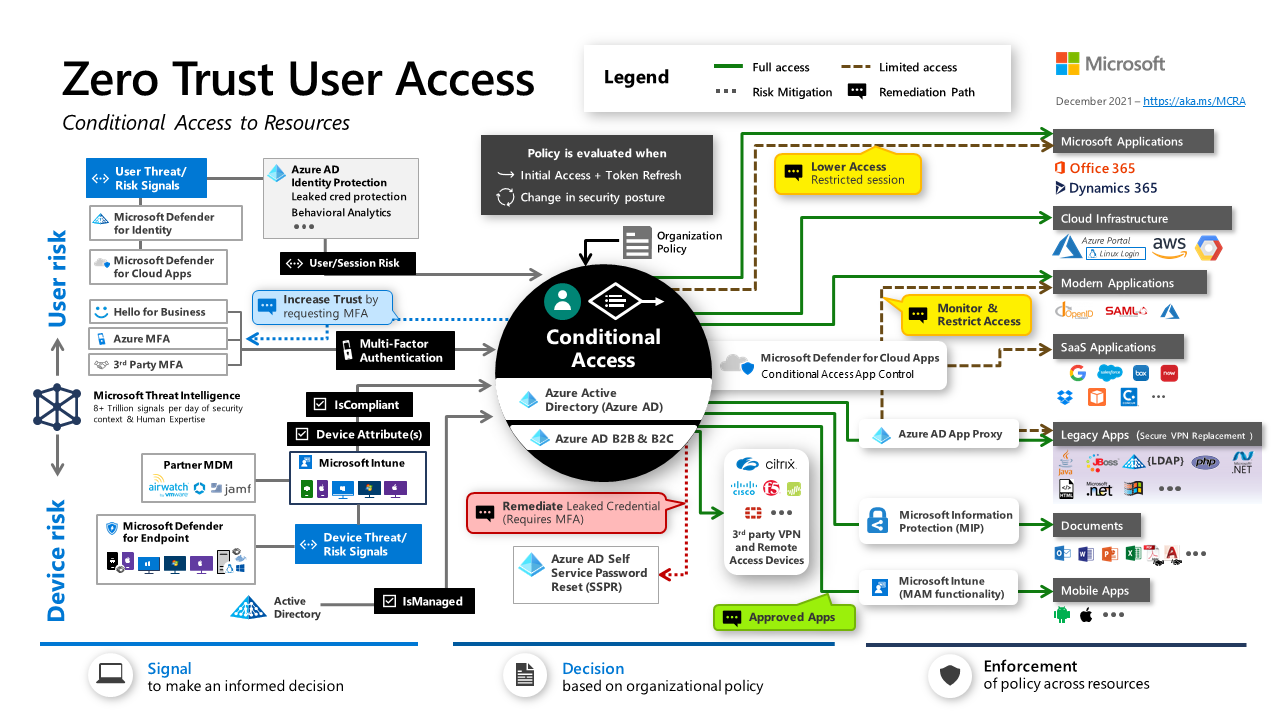
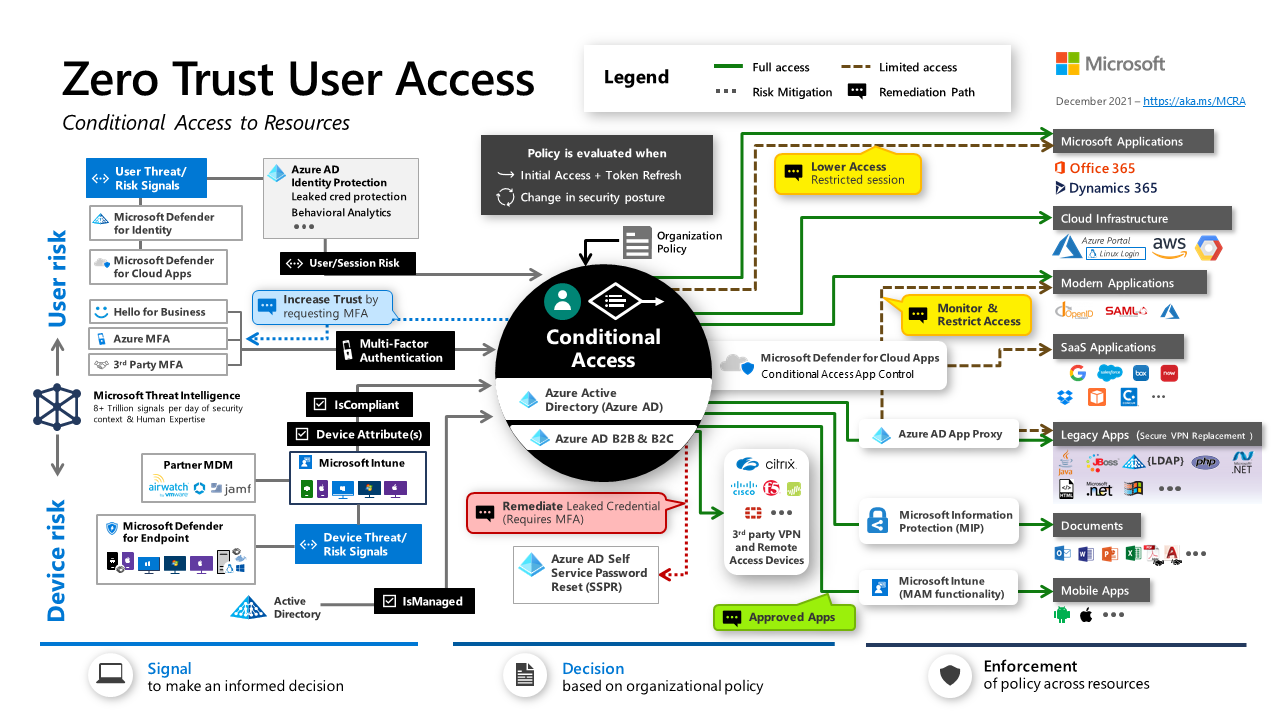
- Microsoft Cybersecurity Reference Architectures (MCRA): A set of detailed technical diagrams that describe Microsoft's cybersecurity capabilities and how they integrate with Microsoft platforms and third-party platforms, such as Microsoft 365, Azure, ServiceNow, Salesforce, AWS and GCP. The MCRA covers various topics such as zero trust user access, security operations, operational technology (OT), multi-cloud and cross-platform capabilities, attack chain coverage, Azure native security controls and security organizational functions.
- SABSA: A framework and methodology for developing business-driven, risk-based and architecture-led security solutions. SABSA stands for Sherwood Applied Business Security Architecture. The framework consists of six layers: contextual (business), conceptual (architecture), logical (design), physical (implementation), component (build) and operational (management). Each layer has a set of attributes that define the security requirements, objectives, functions, services, components and metrics.
- TOGAF: A framework for enterprise architecture that provides a comprehensive approach to planning, designing, implementing and governing an organization's information technology. TOGAF stands for The Open Group Architecture Framework. The framework consists of four domains: business (strategy), data (information), application (system) and technology (infrastructure). Each domain has a set of principles, standards, models and views that guide the architecture development process.
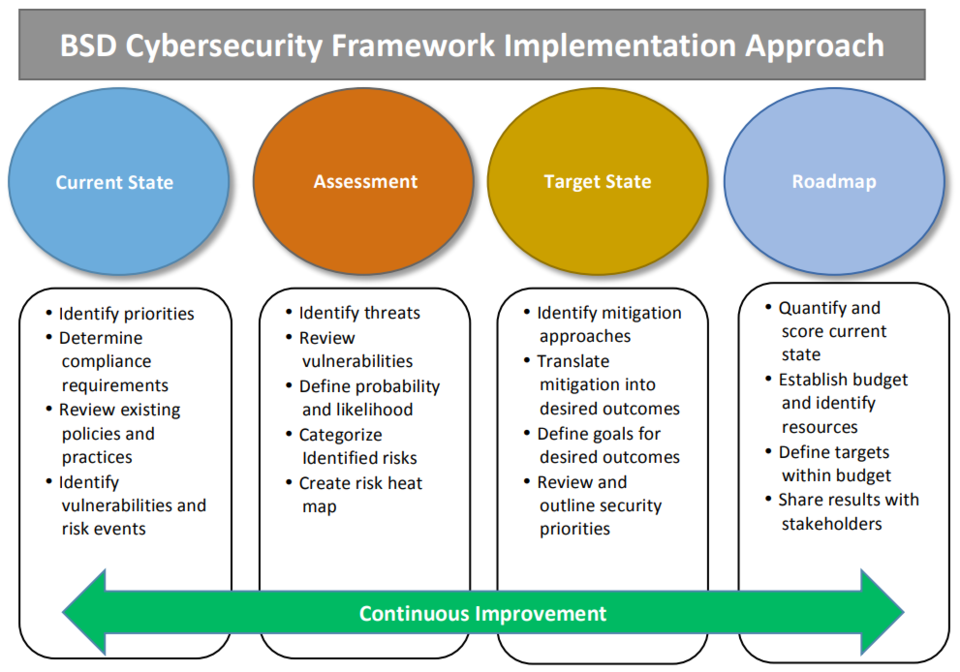
Cybersecurity Roadmaps
A cybersecurity roadmap is a plan or strategy that outlines the steps and actions that an organization needs to take to achieve its security goals and objectives. A cybersecurity roadmap can help organizations to:
- Align their security initiatives with their business vision and mission
- Communicate their security vision and direction to stakeholders
- Prioritize their security investments and resources
- Track their progress and performance against their targets
- Adapt to changing threats, technologies and business needs
Some examples of cybersecurity roadmaps are:
- NIST Cybersecurity Framework Roadmap: A companion document to the NIST CSF that identifies key activities planned for improving and enhancing the CSF. The roadmap is not exhaustive in describing all planned activities within NIST but focuses on high-priority areas for development, alignment and collaboration. The roadmap version 1.1 identifies 14 areas such as confidence mechanisms, cyberattack lifecycle, cybersecurity workforce, cyber supply chain risk management, federal agency cybersecurity alignment, governance and enterprise risk management etc.
- Zero Trust Rapid Modernization Plan (RaMP): A part of the MCRA that provides a practical and actionable approach to implementing zero trust principles and practices in an organization. The RaMP consists of four phases: assess, plan, execute and optimize. Each phase has a set of steps, activities and deliverables that help organizations to define their zero trust vision, identify their current state and gaps, prioritize and implement zero trust capabilities and measure and improve their zero trust maturity.
- CIS Cybersecurity Roadmap: A guide for small and medium-sized businesses (SMBs) to improve their cybersecurity posture using the CIS Controls. The roadmap provides a simple and practical way to implement the CIS Controls based on three levels of security maturity: basic, foundational and organizational. The roadmap also provides tips, resources and tools to help SMBs with their security journey.
Making Sense
|
How to Make Sense of Cybersecurity Frameworks
Frank Kim, Senior Instructor, SANS Institute Security is complex. Explaining it to others is difficult. Frameworks are supposed to help make this easier. But they too are often complex. Learn a model for organizing the vast array of frameworks so that you can simplify the complex world of security and build a more effective program. Hear from Frank Kim, security leader and CISO, as he shares his experiences implementing common frameworks.Learning Objectives:1: Understand how to organize the different types of security frameworks.2: Learn how to use different security frameworks together.3: Discover how to communicate results and drive program execution. Pre-Requisites:Experience building and leading security programs and making decisions on how to structure cybersecurity teams.
|
|
|
|
DEVNET 1158 - Cognitive Threat Analytics - Behavioral Breach Detection via TAXII/STIX API
Speaker: Petr Cernohorsky. Introducing Cognitive Threat Analytics (CTA), Cisco's automated breach detection technology based on statistical modeling and machine learning of network traffic behaviors, whose goal is to identify end-user devices within the monitored network that from network perspective do not represent a communication of a legitimate human user behind their web browser, but actually represent a malware-infected (breached) device establishing its command & control communication to an external malicious infrastructure. The CTA technology produces actionable security intelligence for security operations and threat research to act on. The STIX/TAXII API standards are being used for the security intelligence interchange. An integration is available with the leading SIEM vendors and other STIX/TAXII compliant clients. For all the DevNet Zone 2015 San Diego
|
|
|
The Cybersecurity Framework
Learn more about why organizations of all sizes and types should be using NIST’s voluntary Cybersecurity Framework, which is based on existing standards, guidelines, and best practices. Created through collaboration between industry, academia and government, the flexible Framework helps organizations manage their cybersecurity-related risk.
|
|
|
|
How to Plan for and Implement a Cybersecurity Strategy
Planning and implementing a security strategy to protect a hybrid of on-premises and cloud assets against advanced cybersecurity threats is one of the greatest challenges facing information security organizations today. Join Lex Thomas as he welcomes back Mark Simos to the show as they discuss how Microsoft has built a robust set of strategies and integrated capabilities to help you solve these challenges so that you can build a better understanding how to build an identity security perimeter around your assets. What does a Cybersecurity architecture guide look like? What does the Cybersecurity landscape look like? What does the evolution of IT and Microsoft Security look like? What does a platform security approach look like? Can you describe the benefits of an Integrated Security Experience? How do you measure security success?
|
|
|
Cybersecurity Roadmap: Global Healthcare Security Architecture
Nick H. Yoo, Chief Security Architect, Global Healthcare IT Using NIST cybersecurity framework, one of the largest healthcare IT firms in the US developed global security architecture outlining foundational and differentiated controls for their most sensitive applications.
|
|
|
|
ISMS [ ISO 27001 ] | INFORMATION SECURITY POLICY - How to Write
ISMS [ ISO 27001 ] - How to write Information Security Policy
|
|
Trusted Internet Connections (TIC) 3
|
Trusted Internet Connections (TIC) 3 Webinar
In this webinar, Jim Russo of GSA's Office of Information Technology Category and Sean Connelly of the Cybersecurity And Infrastructure Security Agency break down the Office of Management and Budget's Trusted Internet Connections (TIC) 3.0 guidance. Learn how agencies can adopt popular cloud models while still meeting security standards. Visit https://www.cisa.gov/trusted-internet... to learn more. www.gsa.gov
|
|
|
|
ACT-IAC Networks and Telecommunications COI: Trusted Internet Connection 3.0
ACT-IAC Networks and Telecommunications COI on July 30, 2020 Featured Topic: Trusted Internet Connections 3.0 Presenters: Sean Connelly, Cybersecurity and Infrastructure Security Agency Jim Russo, General Services Administration Joseph Drummond, Cybersecurity and Infrastructure Security Agency
|
|
Zero Trust
YouTube
... Quora
...Google search
...Google News
...Bing News
Zero Trust architecture is a cybersecurity approach that assumes breaches will occur and uses risk-based access controls to limit the damage from an attack. Instead of only guarding an organization’s perimeter, Zero Trust architecture protects each file, email, and network by authenticating every identity and device. Rather than just securing one network, Zero Trust architecture also helps secure remote access, personal devices, and third-party apps. The principles of Zero Trust are: Verify explicitly, Use least privileged access, Assume breach and Require end-to-end encryption.
Never trust, always verify
Part of... software-defined networking (SD-WAN) and Secure Access Service Edge (SASE). SASE delivers wide-area networking with cybersecurity both on-site and in the cloud as DoD expands its reliance on cloud data storage. One of the key tenants of zero trust involves identity. Thunderdome will use identity verification, including public key infrastructure (PKI), which uses a certificate to validate data being sent from one point to another, and identity credentialing and access management (ICAM). ICAM verifies a person’s identity and links them to their allowed access privileges. - Thunderdome hits its targets, DISA moves to next phase of zero trust | Alexandra Lohr - Federal New Network
|
What is Zero Trust Security?
Zero Trust security is no longer just a concept. It has become an essential security strategy that helps organizations protect their valuable data in a “perimeter-everywhere” world. Get the Ultimate Zero Trust Guide: https://bit.ly/2ObCwrS Zero Trust Networks is about having the ability to “Divide and Rule” your network in order to reduce the risk of lateral movement so, in the event of a breach, the threat is easily contained and isolated. Learn more and visit, https://bit.ly/2QFx1U9 for your guide to Absolute Zero Trust security
|
|
|
|
Implementing a zero trust security model at Microsoft | BRK2240
The traditional perimeter-based network defense is obsolete. Perimeter-based networks operate on the assumption that all systems within a network can be trusted. However, today’s increasingly mobile workforce, the migration towards public cloud services, and the adoption of Bring Your Own Device (BYOD) model make perimeter security controls irrelevant. Networks that fail to evolve from traditional defenses are vulnerable to breaches: an attacker can compromise a single endpoint within the trusted boundary and then quickly expand foothold across the entire network. In addition digital transformation will require the security approach change from placing trust in devices attached to corporate networks to an approach where trust is verified with identity and device health validation regardless of connectivity location. In this session, learn how we’re implementing a zero trust model at Microsoft for 150,000 users and 600,000 end points across 120 countries. Learn for Microsoft 365 -- https://aka.ms/GetstartedM365
|
|
|
Zero Trust Architecture: It's All About Identity
The premise of Zero Trust is "don't trust, verify." This approach applies to users, devices, and connectivity sessions and is extremely well suited to supporting remote workforces securely. Zero Trust architecture has been around for many years and embodies this change, yet many organizations have not shifted from the old security models of the past. This has resulted in data loss, credential leak, millions in financial losses and countless hours of lost productivity. In this webinar recording, OCG Principal Architects Frank Urena and Mark Riley discuss: - Defining Zero Trust, Selecting the components of Zero Trust that make the most sense for your organization, Applying Zero Trust in a Microsoft hybrid cloud environment, Where do you begin your journey?
|
|
|
|
The Fallacy of the "Zero-Trust Network"
Paul Simmonds, CISO / CEO, Global Identity Foundation In an industry that loves it marketing buzzwords, “zero trust” is the latest in a long line of buzzwords that have a liberal coating of marketing BS. This session will separate fact from fantasy, marketing hype from practical reality, and explain why although a zero-trust network may be an oxymoron, and zero-trust architectural mindset should be where we all need to end up.Learning Objectives:1: Understand what zero trust actually means.2: Understand the benefits of a correctly implemented zero-trust architecture.3: Understand the business benefits from such an architecture. Pre-Requisites:Networks and security architecture.
|
|
|
Zero Trust on AWS | AWS Events
Zero Trust on AWS | AWS Events
|
|
|
|
Zero Trust Security: Deep Dive into BeyondCorp Enterprise with Google
In this session, Wursta is partnering with Google to deliver a BeyondCorp Enterprise demonstration. This deep dive will show you the product in action so you can apply it to your team, with high-level use cases and expert knowledge on why zero trust is the security framework that’s here to stay.
|
|
|
Cisco Zero Trust Overview
High level insight into how Cisco provides an holisitc approach to Zero-Trust. More than a product and a platform based approach to Zero-Trust.
|
|
|
|
What We Learned Implementing Zero Trust Security at Microsoft
Microsoft has been on a three year journey of implementing Zero Trust. This session will share the lessons that they have learned along the way. This interactive session will walk through the company's core strategy, the five main scenarios they are working on, their design, and how they have organized the teams to ensure that the focus remains were it needs to be on the journey.
|
|
Other Cybersecurity