Difference between revisions of "Cybersecurity"
m (→Open-Source Intelligence - OSINT) |
m |
||
| Line 5: | Line 5: | ||
|description=Helpful resources for your journey with artificial intelligence; videos, articles, techniques, courses, profiles, and tools | |description=Helpful resources for your journey with artificial intelligence; videos, articles, techniques, courses, profiles, and tools | ||
}} | }} | ||
| − | [ | + | [https://www.youtube.com/results?search_query=cybersecurity+security+RSA+malware+detection+artificial+intelligence+ai Youtube search...] |
| − | [ | + | [https://www.google.com/search?q=cybersecurity+security+RSA+malware+detection+deep+machine+learning+ML+ai ...Google search] |
* [[Case Studies]] | * [[Case Studies]] | ||
| Line 19: | Line 19: | ||
* [[Offense - Adversarial Threats/Attacks]] | * [[Offense - Adversarial Threats/Attacks]] | ||
* [[Cybersecurity Frameworks, Architectures & Roadmaps]] | * [[Cybersecurity Frameworks, Architectures & Roadmaps]] | ||
| − | ** [ | + | ** [https://aka.ms/MCRA-MVA Cybersecurity Reference Architecture] | [[Microsoft]] |
* [[Cybersecurity Companies/Products]] | * [[Cybersecurity Companies/Products]] | ||
* [[Cybersecurity: Evaluating & Selling]] | * [[Cybersecurity: Evaluating & Selling]] | ||
| Line 35: | Line 35: | ||
* [[Telecommunications#Physical Layer Security (PLS)|Physical Layer Security (PLS)]] | * [[Telecommunications#Physical Layer Security (PLS)|Physical Layer Security (PLS)]] | ||
* [[Time]] | * [[Time]] | ||
| − | * [ | + | * [https://www.govexec.com/media/gbc_aws_artificial_intelligence_12.20.2018.pdf Government’s AI Odyssey - A Candid Poll on AI and Machine Learning in the Federal Government | Government Business Council - ][[Amazon|AWS]] |
* [[Bayes#Bayesian Poisoning|Bayesian Poisoning]] is a technique used by e-mail spammers to attempt to degrade the effectiveness of spam filters that rely on Bayesian spam filtering | * [[Bayes#Bayesian Poisoning|Bayesian Poisoning]] is a technique used by e-mail spammers to attempt to degrade the effectiveness of spam filters that rely on Bayesian spam filtering | ||
| − | * [ | + | * [https://medium.com/slalom-engineering/detecting-malicious-requests-with-keras-tensorflow-5d5db06b4f28 Detecting Malicious Requests with Keras & TensorFlow | Adam Kusey - Medium] |
| − | * [ | + | * [https://www.csoonline.com/article/3206685/security/best-security-software-how-cutting-edge-tools-tackle-todays-threats.amp.html Best security software: How 12 cutting-edge tools tackle today's threats | CSO] |
* [[Graph]] | * [[Graph]] | ||
** [[Graph#Cybersecurity - Visualization|Cybersecurity - Visualization]] | ** [[Graph#Cybersecurity - Visualization|Cybersecurity - Visualization]] | ||
| − | * [ | + | * [https://www.nextgov.com/emerging-tech/2018/12/iarpa-trying-keep-adversaries-corrupting-ai-tools/153419/ Intelligence Advanced Research Projects Activity (IARPA)Is Trying Keep Adversaries From Corrupting AI Tools ... Could cyber adversaries be training the government’s artificial intelligence tools to fail? | Jack Corrigan - Nextgov] |
| − | ** [ | + | ** [https://www.fbo.gov/index.php?s=opportunity&mode=form&id=93e7534a60d62bc7c44d810c5ea0fdee&tab=core&_cview=0 TrojAI - Office of the Director of National Intelligence Office: Intelligence Advanced Research Projects Activity FedBizOpps.gov] predict whether AI systems have been corrupted through so-called “Trojan attacks.” |
* Adversarial Attacks on [[Graph Convolutional Network (GCN), Graph Neural Networks (Graph Nets), Geometric Deep Learning]] | * Adversarial Attacks on [[Graph Convolutional Network (GCN), Graph Neural Networks (Graph Nets), Geometric Deep Learning]] | ||
| − | * [ | + | * [https://medium.com/syncedreview/breaking-down-the-tencent-2018-cybersecurity-report-26b3befde3f4 Breaking Down the Tencent 2018 Cybersecurity Report] |
| − | * [ | + | * [https://chronicle.security/ Chronicle] combines all the best parts of [[Google]] and X culture |
| − | * [ | + | * [https://pathmind.com/wiki/fraud-detection Fraud and Anomaly Detection | Chris Nicholson - A.I. Wiki pathmind] |
| − | * [ | + | * [https://us-cert.cisa.gov/sites/default/files/FactSheets/NCCIC%20ICS_FactSheet_CSET_S508C.pdf The Cyber Security Evaluation Tool (CSET®) | National Cybersecurity and Communications Integration Center] ...provides a systematic, disciplined, and repeatable approach for evaluating an organization’s security posture |
| − | * [ | + | * [https://www.cyberscoop.com/trickbot-takedown-cyber-command-microsoft/ Cyber Command, [[Microsoft]] take action against Trickbot botnet before Election Day | Shannon Vavra - cyberscoop] |
| − | ** [ | + | ** [https://blogs.microsoft.com/on-the-issues/2020/10/20/trickbot-ransomware-disruption-update/ An update on disruption of Trickbot Tom Burt |] [[Microsoft]] ...The seven remaining servers are not traditional command-and-control servers but rather [[Internet of Things (IoT)]] devices |
| − | ** [ | + | ** [https://www.zdnet.com/article/fbi-warning-trickbot-and-ransomware-attackers-plan-big-hit-on-us-hospitals/ FBI warning: Trickbot and ransomware attackers plan big hit on US hospitals | Liam Tung - ZDNet] ...The FBI, [[Cybersecurity: National Institute of Standards and Technology (NIST) & U.S. Department of Homeland Security (DHS)|CISA]], HHS warning comes two weeks after [[Microsoft]]'s partial takedown of the Trickbot botnet. |
| − | ** [ | + | ** [https://www.cyberscoop.com/ransomware-hospitals-ryuk-fireeye/ European ransomware group strikes US hospital networks, analysts warn | Sean Lyngaas - cyberscoop] ..UNC1878 has been deploying Ryuk ransomware and taking multiple hospital IT networks offline ...suspected ransomware attacks this week on hospitals in New York, Oregon and Vermont, and perhaps other states. |
| − | * [ | + | * [https://www.businessinsider.com/cloudflare-coo-michelle-zatlyn-cybersecurity-enterprisee-tech-transformers-2020-10 Cybersecurity as we know it will be 'a thing of the past in the next decade,' says Cloudflare's COO, as security moves towards a 'water treatment' model | Rosalie Chan - Business Insider] ... cybersecurity systems will weed out bad actors earlier in their attacks |
* [[Watch me Build a Cybersecurity Startup]] | [[Creatives#Siraj Raval|Siraj Raval]] | * [[Watch me Build a Cybersecurity Startup]] | [[Creatives#Siraj Raval|Siraj Raval]] | ||
| − | * [ | + | * [https://fidelissecurity.com/resource/podcast/machine-learning-capabilities-ndr/ Machine-Learning Capabilities within Network Detection & Response (NDR) - Podcast | Fidelis Cybersecurity - COO, Craig Harber, and Data Science Manager, Abhishek Sharma] ...[https://fidelissecurity.com/resources/edu/network-security/extended-detection-response-xdr/ Extended Detection & Response (NDR)] |
| Line 63: | Line 63: | ||
<youtube>UDChsxHx1wc</youtube> | <youtube>UDChsxHx1wc</youtube> | ||
<b>AI-Based, Real-Time Threat Detection at Scale | <b>AI-Based, Real-Time Threat Detection at Scale | ||
| − | </b><br>Cybersecurity remains one of the top sources of risk in the enterprise. This has been exacerbated by the global pandemic, which has forced companies to accelerate digitization initiatives to better support a remote workforce. [[NVIDIA]] Morpheus lets cybersecurity developers and independent software vendors build high-performance pipelines for security workflows with minimal development effort. With Morpheus, enterprises can observe all their data across their entire network and apply Al inferencing and real-time monitoring to all necessary packets and data streams - at a scale previously impossible to achieve. For more information, visit the [ | + | </b><br>Cybersecurity remains one of the top sources of risk in the enterprise. This has been exacerbated by the global pandemic, which has forced companies to accelerate digitization initiatives to better support a remote workforce. [[NVIDIA]] Morpheus lets cybersecurity developers and independent software vendors build high-performance pipelines for security workflows with minimal development effort. With Morpheus, enterprises can observe all their data across their entire network and apply Al inferencing and real-time monitoring to all necessary packets and data streams - at a scale previously impossible to achieve. For more information, visit the [https://developer.nvidia.com/morpheus-cybersecurity Morpheus] web page. |
|} | |} | ||
|<!-- M --> | |<!-- M --> | ||
| Line 108: | Line 108: | ||
<youtube>5c6AADI7Pb4</youtube> | <youtube>5c6AADI7Pb4</youtube> | ||
<b>Wiretapping the Secret Service can be easy and fun | Bryan Seely | TEDxKirkland | <b>Wiretapping the Secret Service can be easy and fun | Bryan Seely | TEDxKirkland | ||
| − | </b><br>In 2014, Bryan Seely hacked the Secret Service and the FBI, and then turned himself in to alert authorities to the problem. He'll tell you what you can do about it in his very entertaining talk. Bryan Seely has garnered a great deal of national attention in the last year. He recognized there were some critical problems with the websites we use most often. He learned that not only is our personal security threatened, but so is our national security. To prove his point, Seely hacked the Secret Service and the FBI last year, and then turned himself in to alert authorities to the problem. He'll tell you what you can do about it in his very entertaining talk. This talk was given at a TEDx event using the TED conference format but independently organized by a local community. Learn more at | + | </b><br>In 2014, Bryan Seely hacked the Secret Service and the FBI, and then turned himself in to alert authorities to the problem. He'll tell you what you can do about it in his very entertaining talk. Bryan Seely has garnered a great deal of national attention in the last year. He recognized there were some critical problems with the websites we use most often. He learned that not only is our personal security threatened, but so is our national security. To prove his point, Seely hacked the Secret Service and the FBI last year, and then turned himself in to alert authorities to the problem. He'll tell you what you can do about it in his very entertaining talk. This talk was given at a TEDx event using the TED conference format but independently organized by a local community. Learn more at https://ted.com/tedx |
|} | |} | ||
|}<!-- B --> | |}<!-- B --> | ||
| Line 125: | Line 125: | ||
<youtube>zGBJ7iH0xOw</youtube> | <youtube>zGBJ7iH0xOw</youtube> | ||
<b>AI gets smart about cybersecurity | <b>AI gets smart about cybersecurity | ||
| − | </b><br>Read the CNET cybersecurity article here - | + | </b><br>Read the CNET cybersecurity article here - https://cnet.co/2gxtOGn Cyberattacks have become more sophisticated and more dangerous. Here's how Las Vegas stays safe. Subscribe to CNET: https://cnet.co/2heRhep Check out our playlists: https://cnet.co/2g8kcf4 Like us on Facebook: https://www.facebook.com/cnet |
|} | |} | ||
|}<!-- B --> | |}<!-- B --> | ||
| Line 134: | Line 134: | ||
<youtube>ca-C3voZwpM</youtube> | <youtube>ca-C3voZwpM</youtube> | ||
<b>How Israel Rules The World Of Cyber Security | VICE on HBO | <b>How Israel Rules The World Of Cyber Security | VICE on HBO | ||
| − | </b><br>U.S. intelligence agencies accuse [[Government Services#Russia|Russia]] of hacking the 2016 presidential election, a Ben Ferguson travels to Tel Aviv to find out how Israel is on its way to becoming the world's top cyber superpower. Subscribe to VICE News here: | + | </b><br>U.S. intelligence agencies accuse [[Government Services#Russia|Russia]] of hacking the 2016 presidential election, a Ben Ferguson travels to Tel Aviv to find out how Israel is on its way to becoming the world's top cyber superpower. Subscribe to VICE News here: https://bit.ly/Subscribe-to-VICE-News Check out VICE News for more: https://vicenews.com Follow VICE News here: Facebook: https://www.facebook.com/vicenews |
|} | |} | ||
|<!-- M --> | |<!-- M --> | ||
| Line 159: | Line 159: | ||
<youtube>hx1vlorz1w4</youtube> | <youtube>hx1vlorz1w4</youtube> | ||
<b>How the Future of Cybersecurity Depends on AI/ML | <b>How the Future of Cybersecurity Depends on AI/ML | ||
| − | </b><br>SparkCognition's Director of Cybersecurity, Rick Pither, discusses the role of artificial intelligence and machine learning in the cyber security landscape. For more information on AI in cybersecurity visit: | + | </b><br>SparkCognition's Director of Cybersecurity, Rick Pither, discusses the role of artificial intelligence and machine learning in the cyber security landscape. For more information on AI in cybersecurity visit: https://bit.ly/2Vdzj0j |
|} | |} | ||
|}<!-- B --> | |}<!-- B --> | ||
| Line 176: | Line 176: | ||
<youtube>B3ZZWx9WUEk</youtube> | <youtube>B3ZZWx9WUEk</youtube> | ||
<b>Introduction to Graphistry | <b>Introduction to Graphistry | ||
| − | </b><br>Graphistry transforms the speed and depth of modern investigations. This unique investigation platform allows analysts to bring together all of their tools and data into a single environment where they can see connections, outliers, progression, and scope of security events. Key capabilities include: - Automatically connects and queries across any and all data sources including SIEMs, Spark, Hadoop, threat feeds, or any source with an API. - Displays data as interactive and intuitive graphs that allow analysts to quickly see important connections, follow leads, and pivot to new data sources on the fly. - Allows analysts to save and share complete investigation workflows as Visual Playbooks that can be reused and embedded wherever they are needed. Learn more at | + | </b><br>Graphistry transforms the speed and depth of modern investigations. This unique investigation platform allows analysts to bring together all of their tools and data into a single environment where they can see connections, outliers, progression, and scope of security events. Key capabilities include: - Automatically connects and queries across any and all data sources including SIEMs, Spark, Hadoop, threat feeds, or any source with an API. - Displays data as interactive and intuitive graphs that allow analysts to quickly see important connections, follow leads, and pivot to new data sources on the fly. - Allows analysts to save and share complete investigation workflows as Visual Playbooks that can be reused and embedded wherever they are needed. Learn more at https://www.graphistry.com |
|} | |} | ||
|}<!-- B --> | |}<!-- B --> | ||
| Line 202: | Line 202: | ||
== Fraud Detection == | == Fraud Detection == | ||
| − | * [ | + | * [https://www.kdnuggets.com/2018/08/introduction-fraud-detection-systems.html Introduction to Fraud Detection Systems | Miguel Gonzalez-Fierro, Microsoft] |
| − | * [ | + | * [https://emerj.com/ai-sector-overviews/ai-for-health-insurance-fraud-detection-current-applications/?utm_term=43496&utm_medium=ai-for-health-insurance-fraud-detection-current-applications%2F&utm_campaign=broadcast&utm_source=email&utm_content=&_ke=eyJrbF9lbWFpbCI6ICJicGVhdEBlcHJvY2Vzc3NvbHV0aW9ucy5jb20iLCAia2xfY29tcGFueV9pZCI6ICJNanhacWcifQ%3D%3D AI for Health Insurance Fraud Detection – Current Applications | Niccolo Mejia] |
{|<!-- T --> | {|<!-- T --> | ||
| Line 228: | Line 228: | ||
<youtube>gCWBFyFTxVU</youtube> | <youtube>gCWBFyFTxVU</youtube> | ||
<b>Build A Complete Project In Machine Learning | Credit Card Fraud Detection 2019 | Eduonix | <b>Build A Complete Project In Machine Learning | Credit Card Fraud Detection 2019 | Eduonix | ||
| − | </b><br>Look what we have for you! Another complete project in Machine Learning! In today's tutorial, we will be building a Credit Card Fraud Detection System from scratch! It is going to be a very interesting project to learn! It is one of the 10 projects from our course For this project, we will be using the several methods of Anomaly detection with Probability Densities. Artificial Intelligence and Machine Learning E-degree - | + | </b><br>Look what we have for you! Another complete project in Machine Learning! In today's tutorial, we will be building a Credit Card Fraud Detection System from scratch! It is going to be a very interesting project to learn! It is one of the 10 projects from our course For this project, we will be using the several methods of Anomaly detection with Probability Densities. Artificial Intelligence and Machine Learning E-degree - https://bit.ly/34tCH6S We will be implementing the two major algorithms namely, 1. A local out wire factor to calculate anomaly scores. |
| − | 2. Isolation forced algorithm. To get started we will first build a dataset of over 280,000 credit card transactions to work on! Get access similar 5 more projects here in this with certification- | + | 2. Isolation forced algorithm. To get started we will first build a dataset of over 280,000 credit card transactions to work on! Get access similar 5 more projects here in this with certification- https://bit.ly/2Q2dX3Q You can access the source code of this tutorial here: https://github.com/eduonix/creditcardML You can even check FREE course on Predict Board Game Reviews with Machine Learning on https://bit.ly/2Wm2uKW Learn Machine Learning By Building Projects -https://bit.ly/2ZNkK5T Machine Learning For Absolute Beginners -https://bit.ly/2Q2pNe7 |
|} | |} | ||
|<!-- M --> | |<!-- M --> | ||
| Line 237: | Line 237: | ||
<youtube>m7htZ7PWQE8</youtube> | <youtube>m7htZ7PWQE8</youtube> | ||
<b>Leveraging Machine Learning for Fraud Analytics (Cloud Next '18) | <b>Leveraging Machine Learning for Fraud Analytics (Cloud Next '18) | ||
| − | </b><br>We will showcase how we can build advance accelerators for Fraud Analytics solutions leveraging [[Google]] Stack. We will demonstrate how these accelerators fill the gaps that exists within other Fraud Analytics solutions currently available in the market today and how it can offer several benefits including real-time processing, increased accuracy, scalable database and high performance. MLAI102 Event schedule | + | </b><br>We will showcase how we can build advance accelerators for Fraud Analytics solutions leveraging [[Google]] Stack. We will demonstrate how these accelerators fill the gaps that exists within other Fraud Analytics solutions currently available in the market today and how it can offer several benefits including real-time processing, increased accuracy, scalable database and high performance. MLAI102 Event schedule https://g.co/next18 Watch more Machine Learning & AI sessions here → https://bit.ly/2zGKfcg Next ‘18 All Sessions playlist https://bit.ly/Allsessions Subscribe to the [[Google]] Cloud channel! → https://bit.ly/NextSub |
|} | |} | ||
|}<!-- B --> | |}<!-- B --> | ||
| Line 243: | Line 243: | ||
= <span id="MITRE ATT&CK™"></span>MITRE ATT&CK™ = | = <span id="MITRE ATT&CK™"></span>MITRE ATT&CK™ = | ||
| − | [ | + | [https://www.youtube.com/results?search_query=MITRE+ATT&CK+threat+cybersecurity+securitydata+center+security+artificial+intelligence+ai Youtube search...] |
| − | [ | + | [https://www.google.com/search?q=MITRE+ATT&CK+threat+cybersecurity+securitydata+center+security+artificial+intelligence+ai ...Google search] |
| − | * [ | + | * [https://mitre-attack.github.io/attack-navigator/enterprise/ ATT&CK™ Navigator |] [https://www.mitre.org/ MITRE] ...measure your threat detection |
| − | * [ | + | * [https://attack.mitre.org/ ATT&CK™ Homepage |] [https://www.mitre.org/ MITRE] |
| − | * [ | + | * [https://attack.mitre.org/resources/ ATT&CK™ Resources |] [https://www.mitre.org/ MITRE] |
| − | * [ | + | * [https://www.varonis.com/blog/mitre-attck-framework-complete-guide/ MITRE ATT&CK™ Framework: Everything You Need to Know | Jeff Petters - Varonis] |
| − | * [ | + | * [https://www.mbsecure.nl/blog/2019/5/dettact-mapping-your-blue-team-to-mitre-attack DETT&CT: MAPPING YOUR BLUE TEAM TO MITRE ATT&CK™ | Marcus Bakker and Ruben Bouman - MB Secure] ...DEtect Tactics, Techniques & Combat Threats |
| − | * [ | + | * [https://redcanary.com/blog/mitre-sub-techniques/ Remapping Red Canary with ATT&CK sub-techniques | B. Donohue, K. Nickels, and M. Graeber] - [https://atomicredteam.io/ Atomic Red Team]; a library of simple tests that every security team can execute to test their defenses. |
* [[Loop#Using the OODA Loop - Purple Team with Cybersecurity|Using the OODA Loop - Purple Team with Cybersecurity]] | * [[Loop#Using the OODA Loop - Purple Team with Cybersecurity|Using the OODA Loop - Purple Team with Cybersecurity]] | ||
| Line 257: | Line 257: | ||
| − | <img src=" | + | <img src="https://attack.mitre.org/theme/images/navigatorss.png" width="1100"> |
| Line 319: | Line 319: | ||
= Open-Source Intelligence - OSINT = | = Open-Source Intelligence - OSINT = | ||
| − | [ | + | [https://www.youtube.com/results?search_query=Open+Source+intelligence+OSINT Youtube search...] |
| − | [ | + | [https://www.google.com/search?q=Open+Source+intelligence+OSINT ...Google search] |
| − | * [ | + | * [https://osintframework.com/ OSINT Framework | Justin Nordine] |
| − | ** [ | + | ** [https://github.com/lockfale/osint-framework OSINT Framework GitHub] |
| − | * [ | + | * [https://www.economist.com/ukraine-osint-pod How has open-source intelligence influenced the war in Ukraine? | The Economist] |
| − | * [ | + | * [https://www.osint.games/ OSINT Games]...a learning-style Capture The Flag (CTF) experience |
** [[Games - Security]] | ** [[Games - Security]] | ||
| − | * [ | + | * [https://academy.tcm-sec.com/p/osint-fundamentals Open-Source Intelligence (OSINT) Fundamentals | TCM Security] |
{|<!-- T --> | {|<!-- T --> | ||
| Line 349: | Line 349: | ||
= Open Source Tools = | = Open Source Tools = | ||
| − | [ | + | [https://www.youtube.com/results?search_query=National+Security+Agency+NSA+Ghidra+open+source+cybersecurity+tools Youtube search...] |
| − | [ | + | [https://www.google.com/search?q=National+Security+Agency+NSA+Ghidra+open+source+cybersecurity+tools ...Google search] |
| − | * [ | + | * [https://www.nsa.gov/ National Security Agency (NSA)] |
| − | ** [ | + | ** [https://github.com/NationalSecurityAgency/ghidra/releases Ghidra] A software reverse engineering (SRE) suite of tools developed by NSA's Research Directorate in support of the Cybersecurity mission [https://ghidra-sre.org/ Ghidra.org] |
| − | ** [ | + | ** [https://www.wired.com/story/nsa-ghidra-open-source-tool/ The NSA Makes Ghidra, a Powerful Cybersecurity Tool, Open Source | Lily Hay Newman - Wired] |
| − | ** [ | + | ** [https://github.com/NationalSecurityAgency/datawave DataWave] is an ingest/query framework that leverages Apache Accumulo to provide fast, secure data access. |
| − | * [ | + | * [https://www.datashieldprotect.com/blog/free-open-source-software-cybersecurity Free Open Source Software Cybersecurity | DataShield] |
| − | * [ | + | * [https://techbeacon.com/app-dev-testing/57-open-source-app-sec-tools-guide-free-application-security-software 47 powerful open-source app sec tools you should consider | Mike Perrow - Vertica - TechBeacon] |
{|<!-- T --> | {|<!-- T --> | ||
| Line 381: | Line 381: | ||
= Data Center Security = | = Data Center Security = | ||
| − | [ | + | [https://www.youtube.com/results?search_query=data+center+security+artificial+intelligence+ai Youtube search...] |
| − | [ | + | [https://www.google.com/search?q=data+center+security+artificial+intelligence+ai ...Google search] |
{|<!-- T --> | {|<!-- T --> | ||
| Line 390: | Line 390: | ||
<youtube>X-0V6bYfTpA</youtube> | <youtube>X-0V6bYfTpA</youtube> | ||
<b>Inside Azure datacenter architecture with Mark Russinovich | BRK3097 | <b>Inside Azure datacenter architecture with Mark Russinovich | BRK3097 | ||
| − | </b><br>Join Mark Russinovich, Azure CTO, to learn how [[Microsoft]] Azure enables intelligent, modern, and innovative applications at scale in the cloud, on-premises, and on the edge. [[Microsoft]] Azure has achieved massive, global scale, with more than 50 announced regions consisting of over 100 datacenters, and it is growing fast. It delivers the promise of cloud computing, including high-availability, extreme performance, and security, by custom designing software and hardware to work best together. Mark takes you on a tour of Azure datacenter architecture and implementation innovations, describing everything from Azure global infrastructure, to how we enable large-scale enterprise scenarios on both cloud and edge, and more. [[Microsoft]] Learn for Azure -- https://aka.ms/IntrotoAzure Find your Tech Community | + | </b><br>Join Mark Russinovich, Azure CTO, to learn how [[Microsoft]] Azure enables intelligent, modern, and innovative applications at scale in the cloud, on-premises, and on the edge. [[Microsoft]] Azure has achieved massive, global scale, with more than 50 announced regions consisting of over 100 datacenters, and it is growing fast. It delivers the promise of cloud computing, including high-availability, extreme performance, and security, by custom designing software and hardware to work best together. Mark takes you on a tour of Azure datacenter architecture and implementation innovations, describing everything from Azure global infrastructure, to how we enable large-scale enterprise scenarios on both cloud and edge, and more. [[Microsoft]] Learn for Azure -- https://aka.ms/IntrotoAzure Find your Tech Community https://aka.ms/FindyourTechCommunity Fast Track -- https://aka.ms/FastrackforAzure |
|} | |} | ||
|<!-- M --> | |<!-- M --> | ||
| Line 398: | Line 398: | ||
<youtube>kd33UVZhnAA</youtube> | <youtube>kd33UVZhnAA</youtube> | ||
<b>[[Google]] Data Center Security: 6 Layers Deep | <b>[[Google]] Data Center Security: 6 Layers Deep | ||
| − | </b><br>Security is one of the most critical elements of our data centers’ DNA. With dozens of data centers globally, security operations means managing a massively complex network. Follow Stephanie Wong, as she journeys to the core of a data center, to show you the six layers of physical security designed to thwart unauthorized access. She’ll meet experts along the way to explore the inner workings of the technology and systems that make [[Google]] Cloud one of the most robust enterprise risk management platforms. Data Centers (Data & Security) → | + | </b><br>Security is one of the most critical elements of our data centers’ DNA. With dozens of data centers globally, security operations means managing a massively complex network. Follow Stephanie Wong, as she journeys to the core of a data center, to show you the six layers of physical security designed to thwart unauthorized access. She’ll meet experts along the way to explore the inner workings of the technology and systems that make [[Google]] Cloud one of the most robust enterprise risk management platforms. Data Centers (Data & Security) → https://goo.gle/2LmkzF3 |
| − | [[Google]] Cloud (Trust & Security)→ | + | [[Google]] Cloud (Trust & Security)→ https://goo.gle/3dFDQNT Follow Stephanie on Twitter→ @swongful Subscribe to [[Google]] Cloud Platform → https://goo.gle/GCP Product: Data Center |
|} | |} | ||
|}<!-- B --> | |}<!-- B --> | ||
| Line 416: | Line 416: | ||
<youtube>CM8O7kJ-faQ</youtube> | <youtube>CM8O7kJ-faQ</youtube> | ||
<b>The MOST SECURE data center in the world (The underground cloud) | <b>The MOST SECURE data center in the world (The underground cloud) | ||
| − | </b><br>The most protected data center in the world is located 150 feet below Kansas City, in the caves known as Subtropolis. Everyone seems to know of a unique location for us to explore next. Let us know YOURS at: | + | </b><br>The most protected data center in the world is located 150 feet below Kansas City, in the caves known as Subtropolis. Everyone seems to know of a unique location for us to explore next. Let us know YOURS at: https://www.offthecuf.com A Flutter Brothers Production Music by Robert Pirogovsky, https://www.robertpirogovsky.com/ Created by Chris and Harris With help from Eric Ford #Technology #thecloud #tech Subscribe to our newsletter: https://www.offthecuf.com/joinus |
|} | |} | ||
|}<!-- B --> | |}<!-- B --> | ||
| Line 425: | Line 425: | ||
<youtube>JgCvam5pKks</youtube> | <youtube>JgCvam5pKks</youtube> | ||
<b>The World’s Most Secure Buildings | <b>The World’s Most Secure Buildings | ||
| − | </b><br>From underground military bunkers and gold reserves to historic and rarely accessed religious archives, we've unlocked the world’s most secure buildings. For more by The B1M subscribe now: | + | </b><br>From underground military bunkers and gold reserves to historic and rarely accessed religious archives, we've unlocked the world’s most secure buildings. For more by The B1M subscribe now: https://ow.ly/GxW7y Go Behind The B1M. Click "JOIN" here - https://bit.ly/2Ru3M6O The B1M Merch store - teespring.com/stores/theb1m Footage and images courtesy of Sarah Scoles, U.S. Air Force, Google Earth,United States Department of Defence, Trevor Hughes, Senior Sergeant Bob Simons of the United States Air Force, Centro Televisivo Vaticano Archivio, John Coffman, Travis Good, Scott Holmes, Federal Reserve Bank of New York, Emil Nordin, Jonathan Nackstrand, Jonas Krantz, Roger Schederin, Ake E-Son Lindman, United States National Parks Services, Official White House Photos by Chuck Kennedy, Andrea Hanks and Pete Souza View this video and more at - https://www.TheB1M.com Like us on Facebook - https://www.facebook.com/TheB1M |
|} | |} | ||
|<!-- M --> | |<!-- M --> | ||
Revision as of 11:51, 5 January 2023
Youtube search... ...Google search
- Case Studies
- Capabilities
- Cybersecurity References
- Offense - Adversarial Threats/Attacks
- Cybersecurity Frameworks, Architectures & Roadmaps
- Cybersecurity Companies/Products
- Cybersecurity: Evaluating & Selling
- (Artificial) Immune System
- 5G Security
- Assured-Positioning, Navigation and Timing (A-PNT)
- AIOps / MLOps
- Games - Security
- Useful Models ...find outliers:
- Physical Layer Security (PLS)
- Time
- Government’s AI Odyssey - A Candid Poll on AI and Machine Learning in the Federal Government | Government Business Council - AWS
- Bayesian Poisoning is a technique used by e-mail spammers to attempt to degrade the effectiveness of spam filters that rely on Bayesian spam filtering
- Detecting Malicious Requests with Keras & TensorFlow | Adam Kusey - Medium
- Best security software: How 12 cutting-edge tools tackle today's threats | CSO
- Graph
- Intelligence Advanced Research Projects Activity (IARPA)Is Trying Keep Adversaries From Corrupting AI Tools ... Could cyber adversaries be training the government’s artificial intelligence tools to fail? | Jack Corrigan - Nextgov
- TrojAI - Office of the Director of National Intelligence Office: Intelligence Advanced Research Projects Activity FedBizOpps.gov predict whether AI systems have been corrupted through so-called “Trojan attacks.”
- Adversarial Attacks on Graph Convolutional Network (GCN), Graph Neural Networks (Graph Nets), Geometric Deep Learning
- Breaking Down the Tencent 2018 Cybersecurity Report
- Chronicle combines all the best parts of Google and X culture
- Fraud and Anomaly Detection | Chris Nicholson - A.I. Wiki pathmind
- The Cyber Security Evaluation Tool (CSET®) | National Cybersecurity and Communications Integration Center ...provides a systematic, disciplined, and repeatable approach for evaluating an organization’s security posture
- Cyber Command, Microsoft take action against Trickbot botnet before Election Day | Shannon Vavra - cyberscoop
- An update on disruption of Trickbot Tom Burt | Microsoft ...The seven remaining servers are not traditional command-and-control servers but rather Internet of Things (IoT) devices
- FBI warning: Trickbot and ransomware attackers plan big hit on US hospitals | Liam Tung - ZDNet ...The FBI, CISA, HHS warning comes two weeks after Microsoft's partial takedown of the Trickbot botnet.
- European ransomware group strikes US hospital networks, analysts warn | Sean Lyngaas - cyberscoop ..UNC1878 has been deploying Ryuk ransomware and taking multiple hospital IT networks offline ...suspected ransomware attacks this week on hospitals in New York, Oregon and Vermont, and perhaps other states.
- Cybersecurity as we know it will be 'a thing of the past in the next decade,' says Cloudflare's COO, as security moves towards a 'water treatment' model | Rosalie Chan - Business Insider ... cybersecurity systems will weed out bad actors earlier in their attacks
- Watch me Build a Cybersecurity Startup | Siraj Raval
- Machine-Learning Capabilities within Network Detection & Response (NDR) - Podcast | Fidelis Cybersecurity - COO, Craig Harber, and Data Science Manager, Abhishek Sharma ...Extended Detection & Response (NDR)
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Contents
Fraud Detection
- Introduction to Fraud Detection Systems | Miguel Gonzalez-Fierro, Microsoft
- AI for Health Insurance Fraud Detection – Current Applications | Niccolo Mejia
|
|
|
|
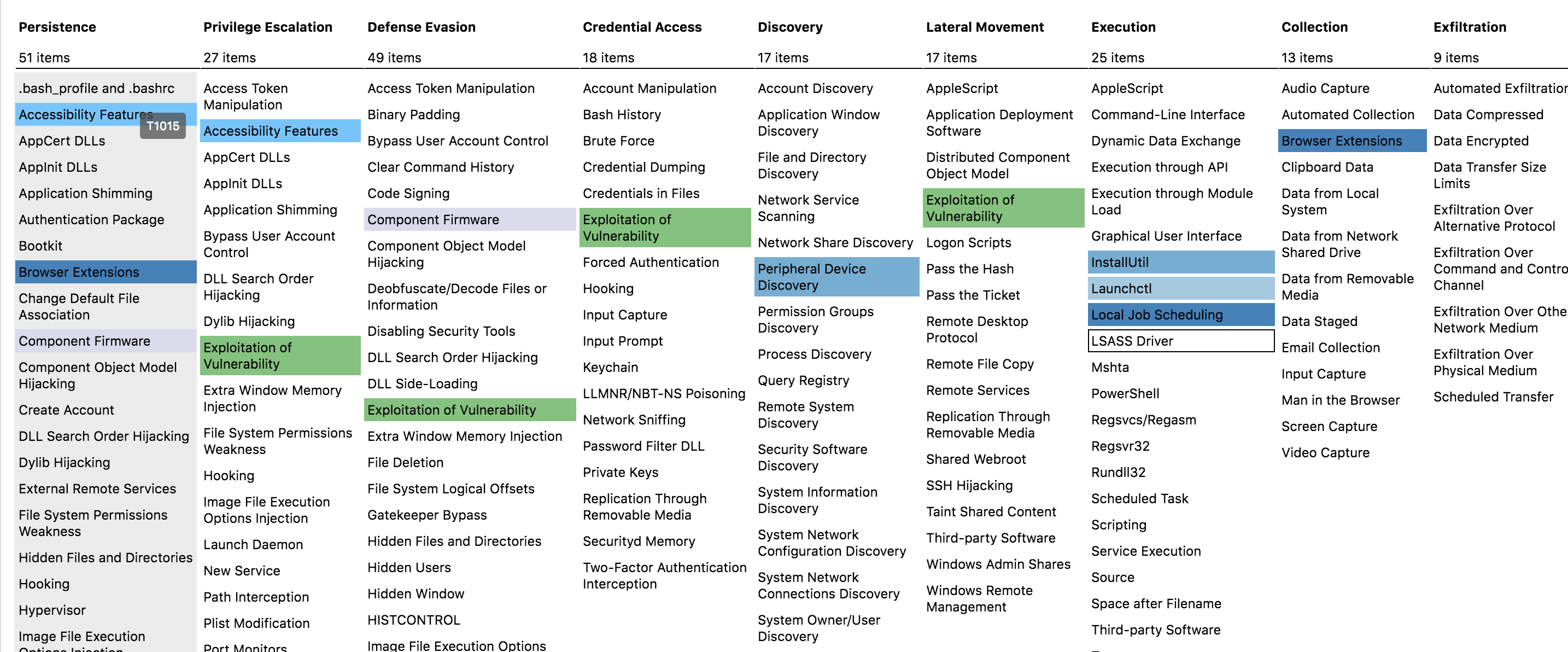
MITRE ATT&CK™
Youtube search... ...Google search
- ATT&CK™ Navigator | MITRE ...measure your threat detection
- ATT&CK™ Homepage | MITRE
- ATT&CK™ Resources | MITRE
- MITRE ATT&CK™ Framework: Everything You Need to Know | Jeff Petters - Varonis
- DETT&CT: MAPPING YOUR BLUE TEAM TO MITRE ATT&CK™ | Marcus Bakker and Ruben Bouman - MB Secure ...DEtect Tactics, Techniques & Combat Threats
- Remapping Red Canary with ATT&CK sub-techniques | B. Donohue, K. Nickels, and M. Graeber - Atomic Red Team; a library of simple tests that every security team can execute to test their defenses.
- Using the OODA Loop - Purple Team with Cybersecurity
knowledge base of adversary tactics and techniques based on real-world observations. The ATT&CK™ knowledge base is used as a foundation for the development of specific threat models and methodologies in the private sector, in government, and in the cybersecurity product and service community.

|
|
|
|
|
|
Open-Source Intelligence - OSINT
Youtube search... ...Google search
- OSINT Framework | Justin Nordine
- How has open-source intelligence influenced the war in Ukraine? | The Economist
- OSINT Games...a learning-style Capture The Flag (CTF) experience
- Open-Source Intelligence (OSINT) Fundamentals | TCM Security
|
|
Open Source Tools
Youtube search... ...Google search
- National Security Agency (NSA)
- Ghidra A software reverse engineering (SRE) suite of tools developed by NSA's Research Directorate in support of the Cybersecurity mission Ghidra.org
- The NSA Makes Ghidra, a Powerful Cybersecurity Tool, Open Source | Lily Hay Newman - Wired
- DataWave is an ingest/query framework that leverages Apache Accumulo to provide fast, secure data access.
- Free Open Source Software Cybersecurity | DataShield
- 47 powerful open-source app sec tools you should consider | Mike Perrow - Vertica - TechBeacon
|
|
Data Center Security
Youtube search... ...Google search
|
|
|
|
|
|