Difference between revisions of "Joint Capabilities Integration and Development System (JCIDS)"
m |
m (→Adaptive Acquisition Framework Methods (Pathways)) |
||
| (7 intermediate revisions by the same user not shown) | |||
| Line 18: | Line 18: | ||
* [[Cybersecurity]] ... [[Open-Source Intelligence - OSINT |OSINT]] ... [[Cybersecurity Frameworks, Architectures & Roadmaps | Frameworks]] ... [[Cybersecurity References|References]] ... [[Offense - Adversarial Threats/Attacks| Offense]] ... [[National Institute of Standards and Technology (NIST)|NIST]] ... [[U.S. Department of Homeland Security (DHS)| DHS]] ... [[Screening; Passenger, Luggage, & Cargo|Screening]] ... [[Law Enforcement]] ... [[Government Services|Government]] ... [[Defense]] ... [[Joint Capabilities Integration and Development System (JCIDS)#Cybersecurity & Acquisition Lifecycle Integration| Lifecycle Integration]] ... [[Cybersecurity Companies/Products|Products]] ... [[Cybersecurity: Evaluating & Selling|Evaluating]] | * [[Cybersecurity]] ... [[Open-Source Intelligence - OSINT |OSINT]] ... [[Cybersecurity Frameworks, Architectures & Roadmaps | Frameworks]] ... [[Cybersecurity References|References]] ... [[Offense - Adversarial Threats/Attacks| Offense]] ... [[National Institute of Standards and Technology (NIST)|NIST]] ... [[U.S. Department of Homeland Security (DHS)| DHS]] ... [[Screening; Passenger, Luggage, & Cargo|Screening]] ... [[Law Enforcement]] ... [[Government Services|Government]] ... [[Defense]] ... [[Joint Capabilities Integration and Development System (JCIDS)#Cybersecurity & Acquisition Lifecycle Integration| Lifecycle Integration]] ... [[Cybersecurity Companies/Products|Products]] ... [[Cybersecurity: Evaluating & Selling|Evaluating]] | ||
| − | * [[ | + | * [[Architectures]] for AI ... [[Generative AI Stack]] ... [[Enterprise Architecture (EA)]] ... [[Enterprise Portfolio Management (EPM)]] ... [[Architecture and Interior Design]] ... <i>[[Enterprise Architecture (EA)#Taxonomy|What is a Capability?]]</i> |
| − | |||
* [[Strategy & Tactics]] ... [[Project Management]] ... [[Best Practices]] ... [[Checklists]] ... [[Project Check-in]] ... [[Evaluation]] ... [[Evaluation - Measures|Measures]] | * [[Strategy & Tactics]] ... [[Project Management]] ... [[Best Practices]] ... [[Checklists]] ... [[Project Check-in]] ... [[Evaluation]] ... [[Evaluation - Measures|Measures]] | ||
| − | * [[Analytics]] ... [[Visualization]] ... [[Graphical Tools for Modeling AI Components|Graphical Tools | + | * [[Analytics]] ... [[Visualization]] ... [[Graphical Tools for Modeling AI Components|Graphical Tools]] ... [[Diagrams for Business Analysis|Diagrams]] & [[Generative AI for Business Analysis|Business Analysis]] ... [[Requirements Management|Requirements]] ... [[Loop]] ... [[Bayes]] ... [[Network Pattern]] |
* [[Development]] ... [[Notebooks]] ... [[Development#AI Pair Programming Tools|AI Pair Programming]] ... [[Codeless Options, Code Generators, Drag n' Drop|Codeless, Generators, Drag n' Drop]] ... [[Algorithm Administration#AIOps/MLOps|AIOps/MLOps]] ... [[Platforms: AI/Machine Learning as a Service (AIaaS/MLaaS)|AIaaS/MLaaS]] | * [[Development]] ... [[Notebooks]] ... [[Development#AI Pair Programming Tools|AI Pair Programming]] ... [[Codeless Options, Code Generators, Drag n' Drop|Codeless, Generators, Drag n' Drop]] ... [[Algorithm Administration#AIOps/MLOps|AIOps/MLOps]] ... [[Platforms: AI/Machine Learning as a Service (AIaaS/MLaaS)|AIaaS/MLaaS]] | ||
| − | * | + | * [https://acqnotes.com/acqnote/acquisitions/jcids-overview AcqNotes:] ... [https://acqnotes.com/search Search/TopicList] ... [https://acqnotes.com/dictionary Dictionary] ... [https://aaf.dau.edu/aaf/policies/ Acquisition Policies | DAU] |
** [https://acqnotes.com/references Main References] | ** [https://acqnotes.com/references Main References] | ||
*** Main Acquisition References: [https://www.dau.edu/tools/dag Website: Defense Acquisition Guidebook (DAG)], [https://acqnotes.com/wp-content/uploads/2014/09/DoD-Directive-704514-PPBE-Process-29-Aug-2017.pdf DOD Directive 7045.14: Program Planning Budget & Execution (PPBE) Process (pdf)], and [https://www.acqnotes.com/Attachments/DAU%20Program%20Managers%20Toolkit.pdf DAU Program Managers Toolkit (pdf)] ... | *** Main Acquisition References: [https://www.dau.edu/tools/dag Website: Defense Acquisition Guidebook (DAG)], [https://acqnotes.com/wp-content/uploads/2014/09/DoD-Directive-704514-PPBE-Process-29-Aug-2017.pdf DOD Directive 7045.14: Program Planning Budget & Execution (PPBE) Process (pdf)], and [https://www.acqnotes.com/Attachments/DAU%20Program%20Managers%20Toolkit.pdf DAU Program Managers Toolkit (pdf)] ... | ||
| Line 144: | Line 143: | ||
==== 10 USC 2373: Procurement for Experimental Purposes: Rapid acquisition tool for fielding and testing new capabilities ==== | ==== 10 USC 2373: Procurement for Experimental Purposes: Rapid acquisition tool for fielding and testing new capabilities ==== | ||
* [https://www.law.cornell.edu/uscode/text/10/2373 10 USC 2373 Procurement for experimental purposes | Legal Information Institute] | * [https://www.law.cornell.edu/uscode/text/10/2373 10 USC 2373 Procurement for experimental purposes | Legal Information Institute] | ||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
= Overview = | = Overview = | ||
| Line 327: | Line 308: | ||
<youtube>4I7kT1dEZFA</youtube> | <youtube>4I7kT1dEZFA</youtube> | ||
<b>Graphs in Government: Achieving Total Cost Visibility for the U.S. Army | <b>Graphs in Government: Achieving Total Cost Visibility for the U.S. Army | ||
| − | </b><br>Maximizing cost visibility is a common goal for large organizations, including the United States Department of Defense. The United States Army is required to track operating and support costs for weapon systems including weapons definition, force structure, inventory, requisitions, maintenance, ammunition and more. That equates to a vast amount of data and growing data management complexities. To address these challenges and achieve total cost visibility, the Army adopted the Neo4j graph database to create, manage, and analyze data relationships across the logistics community. In this webinar, Jason Zagalsky, Federal Account Manager at Neo4j, will provide a brief overview of Neo4j and Graphs In Government, followed by Preston Hendrickson, Principal Systems Analyst at CALIBRE Systems, describing how modernizing its cost tracking system gave the Army the cost visibility needed to meet [[Defense|DOD]] objectives | + | </b><br>Maximizing cost visibility is a common goal for large organizations, including the United States Department of Defense. The United States Army is required to track operating and support costs for weapon systems including weapons definition, force structure, inventory, requisitions, maintenance, ammunition and more. That equates to a vast amount of data and growing data management complexities. To address these challenges and achieve total cost visibility, the Army adopted the Neo4j [[graph]] [[database]] to create, manage, and analyze data relationships across the logistics community. In this webinar, Jason Zagalsky, Federal Account Manager at Neo4j, will provide a brief overview of Neo4j and Graphs In Government, followed by Preston Hendrickson, Principal Systems Analyst at CALIBRE Systems, describing how modernizing its cost tracking system gave the Army the cost visibility needed to meet [[Defense|DOD]] objectives |
|} | |} | ||
|<!-- M --> | |<!-- M --> | ||
Latest revision as of 14:38, 11 July 2024
Youtube search... ...Google search
- Cybersecurity ... OSINT ... Frameworks ... References ... Offense ... NIST ... DHS ... Screening ... Law Enforcement ... Government ... Defense ... Lifecycle Integration ... Products ... Evaluating
- Architectures for AI ... Generative AI Stack ... Enterprise Architecture (EA) ... Enterprise Portfolio Management (EPM) ... Architecture and Interior Design ... What is a Capability?
- Strategy & Tactics ... Project Management ... Best Practices ... Checklists ... Project Check-in ... Evaluation ... Measures
- Analytics ... Visualization ... Graphical Tools ... Diagrams & Business Analysis ... Requirements ... Loop ... Bayes ... Network Pattern
- Development ... Notebooks ... AI Pair Programming ... Codeless, Generators, Drag n' Drop ... AIOps/MLOps ... AIaaS/MLaaS
- AcqNotes: ... Search/TopicList ... Dictionary ... Acquisition Policies | DAU
- Main References
- Main Acquisition References: Website: Defense Acquisition Guidebook (DAG), DOD Directive 7045.14: Program Planning Budget & Execution (PPBE) Process (pdf), and DAU Program Managers Toolkit (pdf) ...
- DOD Directive 5000.01: The Defense Acquisition System - DoD Directives
- DOD Directive 5000.01: The Defense Acquisition System (pdf) - DoD Directives
- CJCS Instruction 3170.01I Charter of The Joint Requirements Oversight Council (JROC) and Implementation of The Joint Capabilities Integration and Development System (JCIDS) (pdf) | Joint Staff - CJCS Directives Library ...This instruction establishes the JCIDS as the process used by the Joint Requirements Oversight Council (JROC) to fulfill its advisory responsibilities to the Chairman of the Joint Chiefs of Staff in identifying, assessing, validating, and prioritizing joint military capability requirements ... AcqNotes
- Website: JCIDS Intellipedia (CAC Required)
- DOD Instruction 5000.02 - Acquisition Process
- DOD Directive 5000.01: The Defense Acquisition System - DoD Directives
- Key Guides and Handbooks: Integrated Master Plan and Integrated Master Schedule Preparation and User Guide (pdf), DAU Systems Engineering Fundamentals (pdf), Test and Evaluation Management Guide (pdf), GAO Cost Estimating Guide (pdf), Draft Naval Aviation Systems Team Acquisition Logistics Support Plan Guide, and Navy DOD Information Assurance Certification and Accreditation Process Handbook (pdf)
- JCIDS Process - Capabilities Based Assessment (CBA)
- Systems Engineering Initial Capabilities Document (ICD)
- Program Management - Business Case Analysis (BCA)
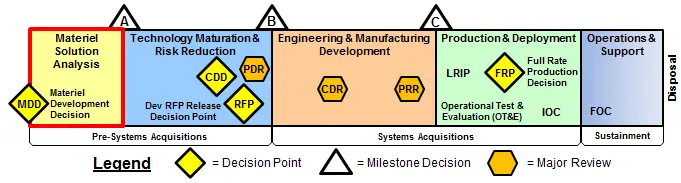
- Acquisition Process Materiel Development Decision (MDD) ...where the Joint Capabilities Integration and Development System (JCIDS) analysis has identified a capability gap/need and a MDD Review has determined a materiel solution is needed. The MDD is the formal point that initiates the ...
- DOD Document Databases: DOD Directives, DoD Instructions, DOD Manuals, Website: ASSIST forDefense Standardization Program (DSP), and EverySpec.com]...Specifications, Standards, Handbooks and Mil-Spec documents
- Main Acquisition References: Website: Defense Acquisition Guidebook (DAG), DOD Directive 7045.14: Program Planning Budget & Execution (PPBE) Process (pdf), and DAU Program Managers Toolkit (pdf) ...
- DOD Guides and Handbooks
- Milestone Requirements Matrix ..tab ACAT I, ACAT II, and ACAT III & Below
- Templates ...main templates that are used in defense acquisitions; need to check with requesting organization
- Main References
- Office of Acquisition Enablers (AE);an organization within the Office of the Under Secretary of Defense (OUSD) for Acquisition & Sustainment (A&S) enabling innovative acquisition approaches
![]()
Integrated Product Support Implementation Roadmap ...List ... Timeline ... Alternate
Contents
- 1 Adaptive Acquisition Framework (AAF)
- 1.1 Adaptive Acquisition Framework Methods (Pathways)
- 2 Overview
- 3 Cybersecurity & Acquisition Lifecycle Integration
- 4 Insights
Adaptive Acquisition Framework (AAF)
- Acquisition Process - DOD Instruction 5000.02
- Adaptive Acquisition Framework | DAU
- The Adaptive Acquisition Framework - Better, Faster, More Tailored (pdf) .. An interview with Stacy Cummings, Principal Deputy for Acquisition Enablers in the Office of the Under Secretary of Defense for Acquisition and Sustainment (A&S)
- Overview of the Adaptive Acquisition Framework | Stacy Cummings, Principal Deputy Assistant Secretary of Defense for Acquisition
- Modernizing DOD Software Production (pdf) | Jeff Boleng, OUSD(A&S), Special Assistant for Software Acquisition
- Milestone Document Identification tool (MDID) ...helps acquisition personnel identify statutory and regulatory program information requirements, as referenced in DODI 5000.85 and DODI 5000.81
The AAF is a major advancement for modern defense acquisition. It is more than a policy update. It is policy re-envisioned and restructured in a framework that encourages critical thinking by program managers in selecting and tailoring the best suited approach or pathway for a particular acquisition. It facilitates more rapid delivery to the point of need. The AAF acquisition pathways provide opportunities for MDAs/DAs and PMs to develop acquisition strategies and employ acquisition processes that match the characteristics of the capability being acquired.

5000.02 Hybrid Program Model A (Hardware Dominant) ...
- Interactive Adaptive Acquisition Framework Tool (ppt)
- Interactive Defense Acquisition Life Cycle Wall Chart (ppt)
- Defense Acquisition Life Cycle Wall Chart; Compliance Baseline (Pre-Tailoring) (pdf)
- Defense Acquisition Life Cycle Wall Chart; Objectives & Contributions with Tailoring, and Compliance with Tailoring (pdf)
Adaptive Acquisition Framework Methods (Pathways)
Urgent Capability Acquisition (UCA) 5000.81
Need identified by Commanders involved in an ongoing contingency operation or emergent need.
- Fielded less than 2 years
- There are three (3) types of of Urgent Needs: 1. Joint Urgent Operational Needs (JUON), 2. Joint Emergent Operational Need (JEON), and 3. Urgent Operational Need (UON)
- JCIDS Process - Urgent Capability Acquisition | AcqNotes
Middle-Tier Acquisition (MTA) 5000.84
Programs that are intended to be completed in a period of 2-5 years via two acquisition pathways.
- Acquisition Process Middle Tier Acquisition (Section 804) | AcqNotes
- Section 804 “Middle Tier of acquisition paths to acquire critical national security capabilities”
- Section 806 “Developing, Prototyping, Developing of Weapons System Components or Technology”
Major Capability Acquisition (MCA) 5000.85
Execute to the standard defense acquisition model with modifications.
- Tailorable
- Major Capability Acquisition | DAU
- Acquisition Process DOD Instruction 5000.85 Major Capability Acquisition ...establishes policy and procedures that guide the acquisition of major capability acquisition programs including: Major Defense Acquisition Programs (MDAPs); Other programs categorized as Acquisition Category (ACAT); Major systems, usually categorized as ACAT II; Automated information systems (AIS) (not managed by other acquisition pathways); and Other capabilities developed via the major capability acquisition pathway.
Software Acquisition
To facilitate rapid and iterative delivery of software capability to the user.
- 6 to 12 months; enable continuous integration and delivery
- Software Acquisition Pathway as the preferred path for acquisition and development of software-intensive systems
- Capability Needs Statements
- The Software Acquisition Pathway (pdf) 3 Jan 20 - Interim Policy
- DOD Software Acquisition: Can DOD Build Weapon Systems Software Better and Faster (pdf) 11 Apr 19 | Carmela B. Rice - Defense Acquisition University
- Example: AEGIS Virtual Twin system
Defense Business Systems (DBS) 5000.75
Business systems are information systems that are operated by, for, or on behalf of the DOD.
Acquisition of Services 5000.74
Acquisition of contracted services from private sector entities by or for the DOD.
- It provides guidance for the acquisition of contracted services from private sector entities by the DOD with
- a total estimated acquisition value in current year dollars at or
- above the Simplified Acquisition Threshold (SAT)
- and acquisition of all Advisory and Assistance Services (A&AS) in support of Research and Development R&D
- or construction activities that are categorized within the knowledge-based services portfolio group
- Acquisition Process - Acquisition of Services | AcqNotes
- DAU's virtual Service Acquisition Mall (SAM) ...create your performance-based service acquisition requirements
Prototyping & Experiments
Early Prototyping 3201.01
Technology or capability that is being matured by the research laboratories.
10 USC 2373: Procurement for Experimental Purposes: Rapid acquisition tool for fielding and testing new capabilities
Overview

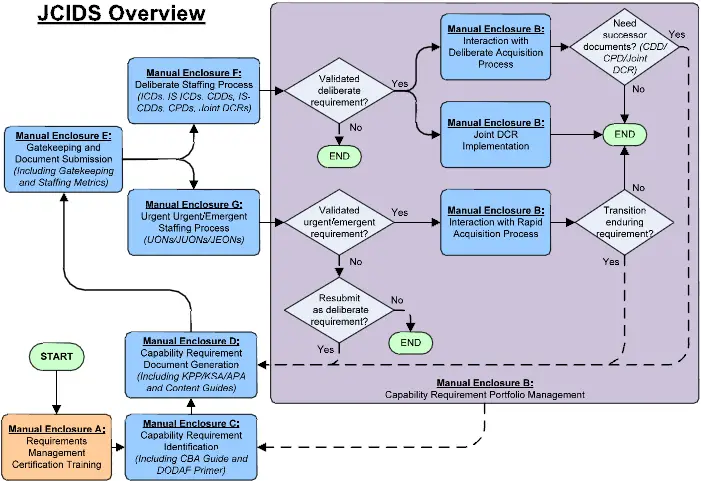 Click: JCIDS Process Flow Chart (pdf)
Click: JCIDS Process Flow Chart (pdf)
AcqNotes Videos
|
|
|
|
U.S. Army
|
|
|
|
Cybersecurity & Acquisition Lifecycle Integration
- Cybersecurity ... OSINT ... Frameworks ... References ... Offense ... NIST ... DHS ... Screening ... Law Enforcement ... Government ... Defense ... Lifecycle Integration ... Products ... Evaluating
- DevSecOps in Government
- Cybersecurity - Visualization
- Cybersecurity Black Card | Defense Acquisition University (DAU)
- Cybersecurity and Acquisition Lifecycle Integration Tool (CALIT) | Defense Acquisition University (DAU)
- The Cybersecurity and Acquisition Life-Cycle Integration Tool | Steve Mills and Tim Denman ...(pdf) - AcqNotes
Understanding what these processes are and how they interact will lead to better acquisition outcomes. The Cybersecurity & Acquisition Lifecycle Integration Tool (CALIT) provides the user the insight into these supporting processes and the ability to visualize how these processes work together to promote cyber resilient weapon systems.

 DOD Cybersecurity Policy Chart | Cyber Security & Information Systems Information Analysis Center ...Changelog
DOD Cybersecurity Policy Chart | Cyber Security & Information Systems Information Analysis Center ...Changelog
- DODI 5000.02T - Operation of the Defense Acquisition System, Enclosure 14; Cybersecurity in the Defense Acquisition System
- Information Technology - Cybersecurity | AcqNotes
- Cybersecurity Test and Evaluation Guidebook (pdf) - Defense Acquisition University (DAU)
- Intelligence & Security - Cybersecurity Strategy ...The strategy is created and maintained by the Program Office and appended to the Program Protection Plan (PPP). It’s required for all ACAT level programs.
- Intelligence & Security - Program Protection Plan (PPP) | AcqNotes
- Outline (doc)
- Template (doc)
- Defense Acquisition Guidebook (DAG) Chapter 9 (pdf) ...provides guidance for the system security engineering (SSE) discipline and Department of Defense (DOD) program protection for defense acquisition programs. The program manager (PM) and the systems engineer (SE) should use DAG
- Intelligence & Security - System Security Engineering (SSE) | AcqNotes ...Systems Security Engineering (SSE) is an element of Systems Engineering (SE) that applies scientific and engineering principles in a standardized, repeatable, and efficient manner to identify security vulnerabilities, requirements, and methods of verifications that minimize risks. SSE delivers systems that satisfy stakeholder security needs for weapon system operation in today’s cyber-contested environments.
- Cyber Threat Analysis
- Intelligence & Security - Validated Online Lifecycle Threat (VOLT) ...The VOLT Reports involve the application of threat modules, and are to be written to articulate the relevance of each module to a specific acquisition program or planned capability. Note: The STAR was replaced by the VOLT
- DODI 5200.39, Critical Program Information (CPI) Identification and Protection Within Research, Development, Test and Evaluation (RDT&E) (pdf)
- DODI 5200.44, Protection of Mission Critical Functions to Achieve Trusted Systems and Networks (TSN) (pdf)
|
|
Insights
|
|
|
|
Center for Strategic & International Studies
|
|