Difference between revisions of "Telecommunications"
m (→Software-Defined Networking (SDN)) |
m |
||
| Line 19: | Line 19: | ||
* [[Telecommunications]] ... [[Computer Networks]] ... [[Telecommunications#5G|5G]] ... [[Satellite#Satellite Communications|Satellite Communications]] ... [[Quantum#Quantum Internet / Communications|Quantum Internet]] ... [[Agents#Communication | Agents]] ... [[AI Generated Broadcast Content|AI Broadcast; Radio, Stream, TV]] | * [[Telecommunications]] ... [[Computer Networks]] ... [[Telecommunications#5G|5G]] ... [[Satellite#Satellite Communications|Satellite Communications]] ... [[Quantum#Quantum Internet / Communications|Quantum Internet]] ... [[Agents#Communication | Agents]] ... [[AI Generated Broadcast Content|AI Broadcast; Radio, Stream, TV]] | ||
* [[Cybersecurity]] ... [[Open-Source Intelligence - OSINT |OSINT]] ... [[Cybersecurity Frameworks, Architectures & Roadmaps | Frameworks]] ... [[Cybersecurity References|References]] ... [[Offense - Adversarial Threats/Attacks| Offense]] ... [[National Institute of Standards and Technology (NIST)|NIST]] ... [[U.S. Department of Homeland Security (DHS)| DHS]] ... [[Screening; Passenger, Luggage, & Cargo|Screening]] ... [[Law Enforcement]] ... [[Government Services|Government]] ... [[Defense]] ... [[Joint Capabilities Integration and Development System (JCIDS)#Cybersecurity & Acquisition Lifecycle Integration| Lifecycle Integration]] ... [[Cybersecurity Companies/Products|Products]] ... [[Cybersecurity: Evaluating & Selling|Evaluating]] | * [[Cybersecurity]] ... [[Open-Source Intelligence - OSINT |OSINT]] ... [[Cybersecurity Frameworks, Architectures & Roadmaps | Frameworks]] ... [[Cybersecurity References|References]] ... [[Offense - Adversarial Threats/Attacks| Offense]] ... [[National Institute of Standards and Technology (NIST)|NIST]] ... [[U.S. Department of Homeland Security (DHS)| DHS]] ... [[Screening; Passenger, Luggage, & Cargo|Screening]] ... [[Law Enforcement]] ... [[Government Services|Government]] ... [[Defense]] ... [[Joint Capabilities Integration and Development System (JCIDS)#Cybersecurity & Acquisition Lifecycle Integration| Lifecycle Integration]] ... [[Cybersecurity Companies/Products|Products]] ... [[Cybersecurity: Evaluating & Selling|Evaluating]] | ||
| + | * [[Cybersecurity Frameworks, Architectures & Roadmaps#Zero Trust|Zero Trust]] | ||
* [[Time]] ... [[Time#Positioning, Navigation and Timing (PNT)|PNT]] ... [[Time#Global Positioning System (GPS)|GPS]] ... [[Causation vs. Correlation#Retrocausality| Retrocausality]] ... [[Quantum#Delayed Choice Quantum Eraser|Delayed Choice Quantum Eraser]] ... [[Quantum]] | * [[Time]] ... [[Time#Positioning, Navigation and Timing (PNT)|PNT]] ... [[Time#Global Positioning System (GPS)|GPS]] ... [[Causation vs. Correlation#Retrocausality| Retrocausality]] ... [[Quantum#Delayed Choice Quantum Eraser|Delayed Choice Quantum Eraser]] ... [[Quantum]] | ||
** [[Time#Software-defined Global Navigation Satellite Systems (GNSS)|Software-defined Global Navigation Satellite Systems (GNSS)]] | ** [[Time#Software-defined Global Navigation Satellite Systems (GNSS)|Software-defined Global Navigation Satellite Systems (GNSS)]] | ||
Revision as of 10:53, 14 July 2023
Youtube search... ...Google search
- Telecommunications ... Computer Networks ... 5G ... Satellite Communications ... Quantum Internet ... Agents ... AI Broadcast; Radio, Stream, TV
- Cybersecurity ... OSINT ... Frameworks ... References ... Offense ... NIST ... DHS ... Screening ... Law Enforcement ... Government ... Defense ... Lifecycle Integration ... Products ... Evaluating
- Zero Trust
- Time ... PNT ... GPS ... Retrocausality ... Delayed Choice Quantum Eraser ... Quantum
- Ericsson launches unique AI functionality to boost radio access networks
- Deepsig pioneering the application of deep learning to wireless
- How Machine Learning Is Creating New Opportunities In The Telecommunications Industry | Julie Stoughton - Digitalist Magazine
- Top 10 Data Science Use cases in Telecom | Igor Bobriakov - Medium
Contents
Cognitive Radio (CR) / Software-defined radio (SDR)
Software-defined radio (SDR) is a radio communication system where components that have been traditionally implemented in hardware (e.g. mixers, filters, amplifiers, modulators/demodulators, detectors, etc.) are instead implemented by means of software on a personal computer or embedded system. Software radios have significant utility for the military and cell phone services, both of which must serve a wide variety of changing radio protocols in real time. In the long term, software-defined radios are to become the dominant technology in radio communications. SDRs, along with software defined antennas are the enablers of the cognitive radio.
GNU Radio
is a free & open-source software development toolkit that provides signal processing blocks to implement software radios. It can be used with readily-available low-cost external RF hardware to create software-defined radios, or without hardware in a simulation-like environment.
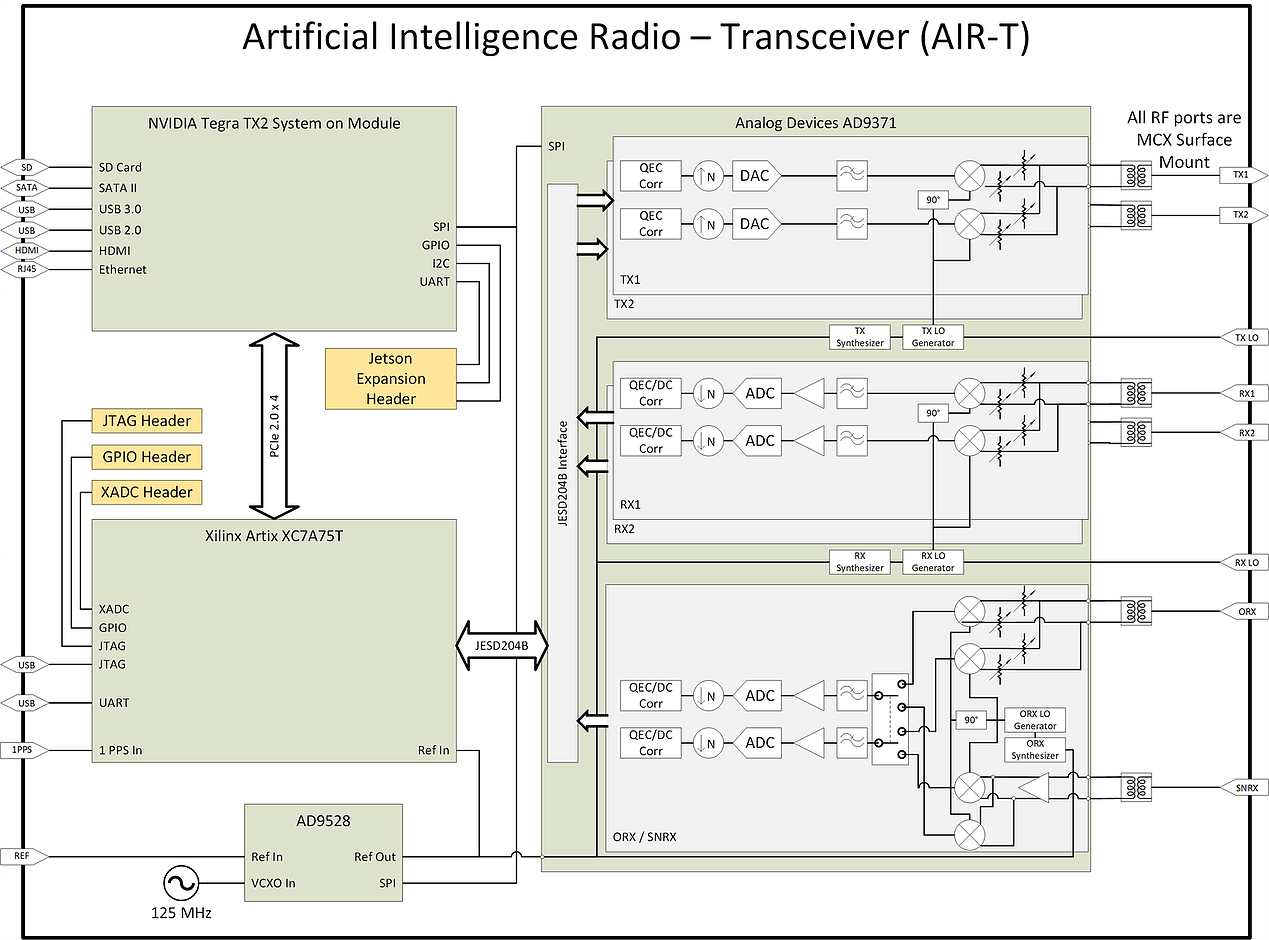
Deepwave Digital Systems
Enabling deep learning and AI at the edge of wireless systems. GPUs are extremely well suited for processes that are highly parallel. The Fast Fourier Transform (FFT) is one of the most common techniques in signal processing and happens to be a highly parallel algorithm. In this blog post the Deepwave team walks you though how to leverage the embedded GPU built into the AIR-T to perform high-speed FFTs without the computational bottleneck of a CPU and without having to experience the long development cycle associated with writing VHDL code for FPGAs. By leveraging the GPU on the AIR-T, you get the best of both worlds: fast development time and high speed processing. A familiar tool to anyone working in the wireless domain, GNU Radio allows signal processing experts to tie together blocks of functionality using an intuitive GUI. Many of the “in the weeds” details regarding the software implementation are well abstracted so the user can focus on the algorithm instead.Once an algorithm has been optimized (or a pre-trained algorithm has been downloaded by a 3rd party), the user will reference it in Deepwave’s GR-WAVELEARNER software that provides a TensorRT Inference block for GNU Radio Companion (GRC)
Software-Defined Networking (SDN)
YouTube ... Quora ... Google search ... Google News ... Bing News
Artificial Intelligence (AI) can assist Software-Defined Networking (SDN) in several ways. One of the main benefits of AI in SDN is the ability to automate network management tasks, which can help to reduce the workload on network administrators and improve network performance. AI can be used to analyze network traffic patterns and predict network failures or congestion, allowing network administrators to take proactive measures to prevent these issues from occurring. AI can also be used to optimize network traffic routing and load balancing, which can improve network performance and reduce latency.
Another way that AI can assist SDN is by enabling more intelligent network security. AI can be used to detect and respond to security threats in real-time, allowing network administrators to quickly identify and mitigate potential security breaches. AI can also be used to analyze network traffic patterns and identify anomalies that may indicate a security threat.
AI can also assist SDN in network optimization. AI algorithms can be used to optimize network traffic routing and load balancing, which can improve network performance and reduce latency. AI can also be used to optimize network resource allocation, ensuring that network resources are allocated efficiently and effectively.
SDN & SD-WAN
Software-Defined Networking (SDN) is an approach to network management that enables dynamic, programmatically efficient network configuration in order to improve network performance and monitoring. SDN is meant to address the fact that the static architecture of traditional networks is decentralized and complex while current networks require more flexibility and easy troubleshooting. SDN suggests to centralize network intelligence in one network component by disassociating the forwarding process of network packets (data plane) from the routing process (control plane). The control plane consists of one or more controllers which are considered as the brain of SDN network. The data plane is composed of OpenFlow-enabled switches which are responsible for the packet forwarding between hosts. The communication between the control and data planes is through the OpenFlow protocol.
SD-WAN (Software-Defined Wide Area Network) is an extension of SDN that applies SDN principles to WAN connections. SD-WAN simplifies the management and operation of a WAN by decoupling the networking hardware from its control mechanism. This concept is similar to how software-defined networking implements virtualization technology to improve data center management and operation. A key application of SD-WAN is to allow companies to build higher-performance WANs using lower-cost and commercially available Internet access, enabling businesses to partially or wholly replace more expensive private WAN connection technologies such as MPLS
Machine learning solving practical problems in Communications
Physical Layer Security (PLS)
Youtube search... ...Google search
Physical layer security (PLS) has emerged as a new concept and powerful alternative that can complement and may even replace encryption-based approaches, which entail many hurdles and practical problems for future wireless systems. The basic idea of PLS is to exploit the characteristics of the wireless channel and its impairments including noise, fading, interference, dispersion, diversity, etc. in order to ensure the ability of the intended user to successfully perform data decoding while preventing eavesdroppers from doing so. Thus, the main design goal of PLS is to increase the performance difference between the link of the legitimate receiver and that of the eavesdropper by using well-designed transmission schemes. Physical Layer Security for Downlink NOMA: Requirements, Merits, Challenges, and Recommendations | H. Furqan, J. Hamamreh, and H. Arslan
Waveform
Youtube search... ...Google search
5G
YouTube search... ...Google search
- Telecommunications ... Computer Networks ... 5G ... Satellite Communications ... Quantum Internet ... Agents ... AI Broadcast; Radio, Stream, TV
- Immersive Reality ... Metaverse ... Digital Twin ... Internet of Things (IoT) ... Transhumanism
- 3rd Generation Partnership Project (3GPP) ...unites [Seven] telecommunications standard development organizations: ARIB, ATIS, CCSA, ETSI, TSDSI, TTA, TTC
- Internet Engineering Taskforce (IETF)
- What is 5G? | NIST
- European Telecommunications Standards Institute (ETSI) ISG Network Functions Virtualisation (NFV) - ETSI Industry Specification Group
- China Global Television Network (CGTN) | Wikipedia
- 5G + Cloud + AI: Huawei Works with Carriers to Power New ICT Infrastructure | Huawei - PR Newswire
- Armed Forces Communications and Electronics Association ...communications, information technology, intelligence and security
- MIMO | Wikipedia
|
|
|
|
5G Security
YouTube search... ...Google search
Three-step approach to reach a high level of intelligent security management. How to master E2E network security when introducing 5G core | Kari-Pekka Perttula - Ericsson
- Dynamic: Introduce automated security policy configuration and compliance monitoring
- Cognitive: Automated threat and vulnerability detection assisted with ML /AI
- Intelligent: Repeatable, adaptive and holistic security management with threat intelligence. This provides end-to-end visibility for business-related security risks, and actions can be directed via automated workflows to mitigate risks faster.
Threat Model: STRIDE | Wikipedia The threats are:
- Spoofing
- Tampering
- Repudiation
- Information disclosure (breach or data leak)
- Denial of service
- Elevation of privilege]
|
|
|
|
|
|
5G Testing
YouTube search... ...Google search
- Model_Monitoring
- DOD Kicks Off World’s Largest Dual-Use 5G Testing Effort | C. Todd Lopez - DOD News ...AT&T, Booz Allen Hamilton, Deloitte Consulting LLP, Ericsson, Federated Wireless, GBL System Corp., General Dynamics Mission Systems, Inc., GE Research, Key Bridge Wireless LLC, KPMG LLP, Nokia, Oceus Networks, Scientific Research Corporation, Shared Spectrum Company and Vectrus Mission Solutions Corporation.
|
|
Virtualization - Dynamic Spectrum Sharing (DSS)
Youtube search... ...Google search ...Google News
- Telecommunications
- Computer Networks
- Defense
- How to Know if You’re Ready to Deploy a Dark Fiber Network | Rob Coenen - Lightwave ...unused or under-utilized fiber infrastructure (including fibers, cabling, and repeaters) that was laid as part of a hedge against exponential growth in data use.
Spectrum Sharing utilizes virtualization to partition optical spectrum
|
|
|
|