Difference between revisions of "Telecommunications"
m (→5G) |
m (→5G Security) |
||
| Line 87: | Line 87: | ||
= <span id="5G Security"></span>5G Security = | = <span id="5G Security"></span>5G Security = | ||
| + | [http://www.youtube.com/results?search_query=5G+security+deep+machine+learning+ML+artificial+intelligence+ai YouTube search...] | ||
| + | [http://www.google.com/search?q=5G+security+deep+machine+learning+ML+artificial+intelligence+ai ...Google search] | ||
Three-step approach to reach a high level of intelligent security management. [http://www.ericsson.com/en/blog/2020/10/how-to-master-e2e-network-security-when-introducing-5g-core How to master E2E network security when introducing 5G core | Kari-Pekka Perttula - Ericsson] | Three-step approach to reach a high level of intelligent security management. [http://www.ericsson.com/en/blog/2020/10/how-to-master-e2e-network-security-when-introducing-5g-core How to master E2E network security when introducing 5G core | Kari-Pekka Perttula - Ericsson] | ||
Revision as of 09:51, 1 October 2020
Youtube search... ...Google search
- Case Studies
- Virtualization - Dynamic Spectrum Sharing (DSS)
- Ericsson launches unique AI functionality to boost radio access networks
- Deepsig pioneering the application of deep learning to wireless
- How Machine Learning Is Creating New Opportunities In The Telecommunications Industry | Julie Stoughton - Digitalist Magazine
- Top 10 Data Science Use cases in Telecom | Igor Bobriakov - Medium
Contents
Cognitive Radio (CR) / Software-defined radio (SDR)
Software-defined radio (SDR) is a radio communication system where components that have been traditionally implemented in hardware (e.g. mixers, filters, amplifiers, modulators/demodulators, detectors, etc.) are instead implemented by means of software on a personal computer or embedded system. Software radios have significant utility for the military and cell phone services, both of which must serve a wide variety of changing radio protocols in real time. In the long term, software-defined radios are to become the dominant technology in radio communications. SDRs, along with software defined antennas are the enablers of the cognitive radio.
GNU Radio
is a free & open-source software development toolkit that provides signal processing blocks to implement software radios. It can be used with readily-available low-cost external RF hardware to create software-defined radios, or without hardware in a simulation-like environment.
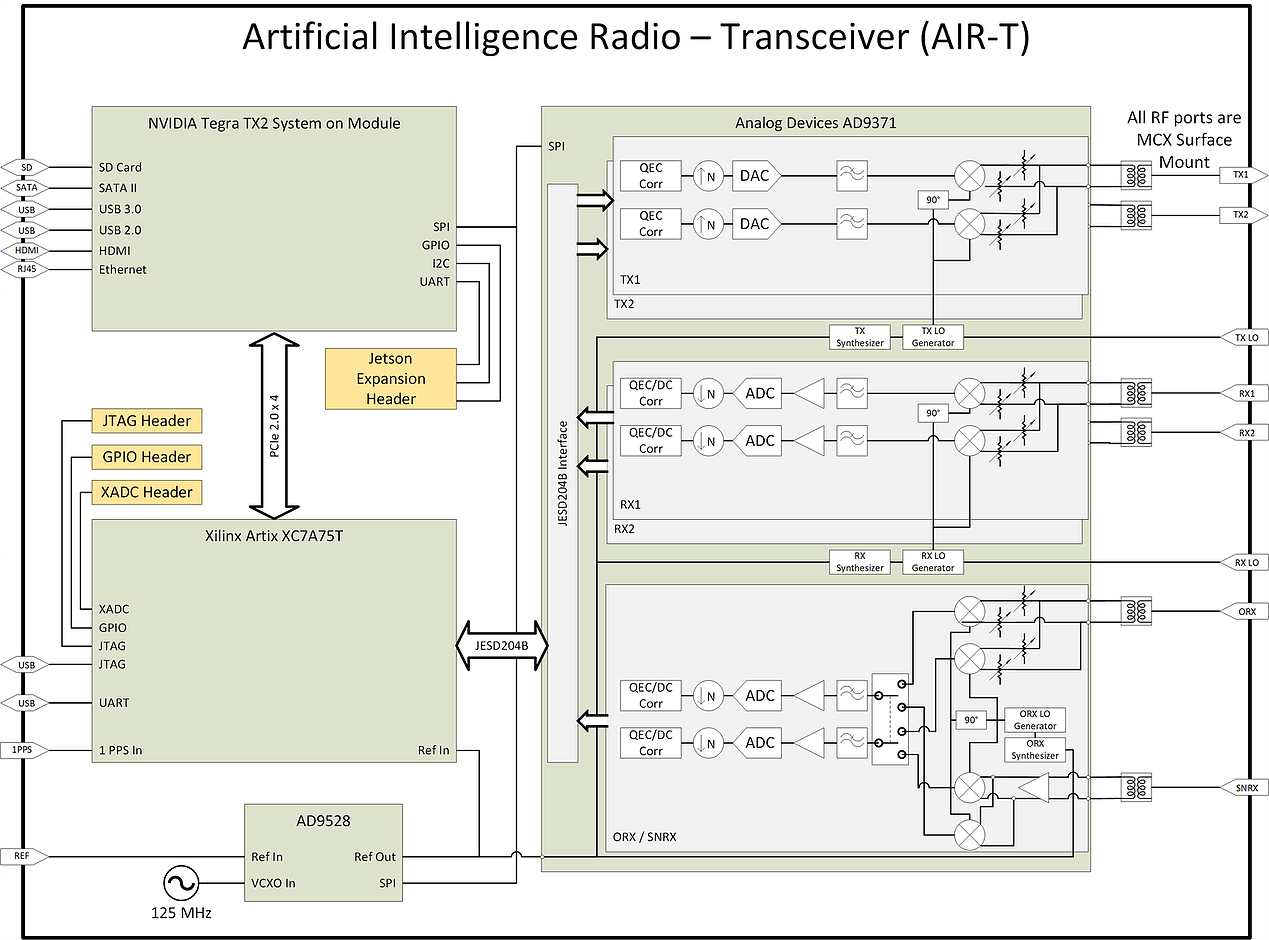
Deepwave Digital Systems
Enabling deep learning and AI at the edge of wireless systems. GPUs are extremely well suited for processes that are highly parallel. The Fast Fourier Transform (FFT) is one of the most common techniques in signal processing and happens to be a highly parallel algorithm. In this blog post the Deepwave team walks you though how to leverage the embedded GPU built into the AIR-T to perform high-speed FFTs without the computational bottleneck of a CPU and without having to experience the long development cycle associated with writing VHDL code for FPGAs. By leveraging the GPU on the AIR-T, you get the best of both worlds: fast development time and high speed processing. A familiar tool to anyone working in the wireless domain, GNU Radio allows signal processing experts to tie together blocks of functionality using an intuitive GUI. Many of the “in the weeds” details regarding the software implementation are well abstracted so the user can focus on the algorithm instead.Once an algorithm has been optimized (or a pre-trained algorithm has been downloaded by a 3rd party), the user will reference it in Deepwave’s GR-WAVELEARNER software that provides a TensorRT Inference block for GNU Radio Companion (GRC)
Machine learning solving practical problems in Communications
5G
YouTube search... ...Google search
- Internet of Things (IoT)
- China Global Television Network (CGTN) | Wikipedia
- 5G + Cloud + AI: Huawei Works with Carriers to Power New ICT Infrastructure | Huawei - PR Newswire
|
|
5G Security
YouTube search... ...Google search
Three-step approach to reach a high level of intelligent security management. How to master E2E network security when introducing 5G core | Kari-Pekka Perttula - Ericsson
- Dynamic: Introduce automated security policy configuration and compliance monitoring
- Cognitive: Automated threat and vulnerability detection assisted with ML /AI
- Intelligent: Repeatable, adaptive and holistic security management with threat intelligence. This provides end-to-end visibility for business-related security risks, and actions can be directed via automated workflows to mitigate risks faster.